New Malware Highlights Increased Systematic Targeting of Network Infrastructure
The enterprise attack surface has undergone a fundamental shift. Over recent years, threat actors, ranging from sophisticated nation-state APTs to financially motivated ransomware groups, have increased the frequency of systematic exploitation of network infrastructure. Eclypsium, Verizon, Google, and others have extensively documented this trend.
New malware samples captured by Eclypsium highlight that the targeting of network infrastructure, especially, but not limited to Fortinet devices, is not exclusive to nation state APTs, but is also being leveraged by crypto-mining operations.
Eclypsium Captures Samples from Two Undocumented Malware Variants
On March 6, 2026, Eclypsium captured new samples of a previously undocumented malware strains:
- CondiBot (DDoS Botnet Variant): An evolution of the Mirai-derived Condi DDoS botnet, this new sample was found to be previously unreported on major threat intelligence platforms. It is a multi-architecture binary (written in C) designed to turn compromised Linux devices into nodes for large-scale network attacks.
- “Monaco” (SSH Scanner & Crypto Miner): An active, multi-architecture cryptojacking operation that targets servers, IoT devices, routers, and network devices by brute-forcing weak SSH credentials, harvesting hundreds of SSH servers and sending credentials back to its C2 servers.
Technical Details
CondiBot Variant
Condibot is a DDoS botnet executor. Its goal is to turn compromised linux devices into remotely controlled nodes capable of launching large-scale network attacks.
Further analysis concluded it does not only attack Fortinet but impacts other network device vendors. It is a generic Linux Botnet agent that tries multiple download methods across multiple filesystems with a variety of architecture payloads for arm, mips and x86. It can work on any vulnerable linux device regardless of the vendor.
Basic details about the CondiBot variant are here. For further details and file hashes, please download our full report.
| Malware Family | CondiBot (Mirai derivate) |
| Filename | executor |
| File Hash | • 98e6884ae15a4f6c0142d9e5edd09d596090a7ea5bbcb642da7f1a6536ee0dca executor.arm• 92d8909813dbe7b5471e60fc08f18a1973adcc04b3489ae3b0b667bfbfd7c0e0 executor.arm5 |
| File Type | ELF 64-bit x86_64, statically linked stripped |
| String Artifacts | condi, condibot, CondiBot, condinetwork, condinet, qtxbot |
| Architectural Variants | arm, arm5. arm6. arm7, mips, x86, x86_64 |
| C2 IP Address | 65.222.202.53 (not active) |
| C2 Port | 80 (0x5000) |
| Listener Port | 17664 (0x4500) |
Mechanism of Attack
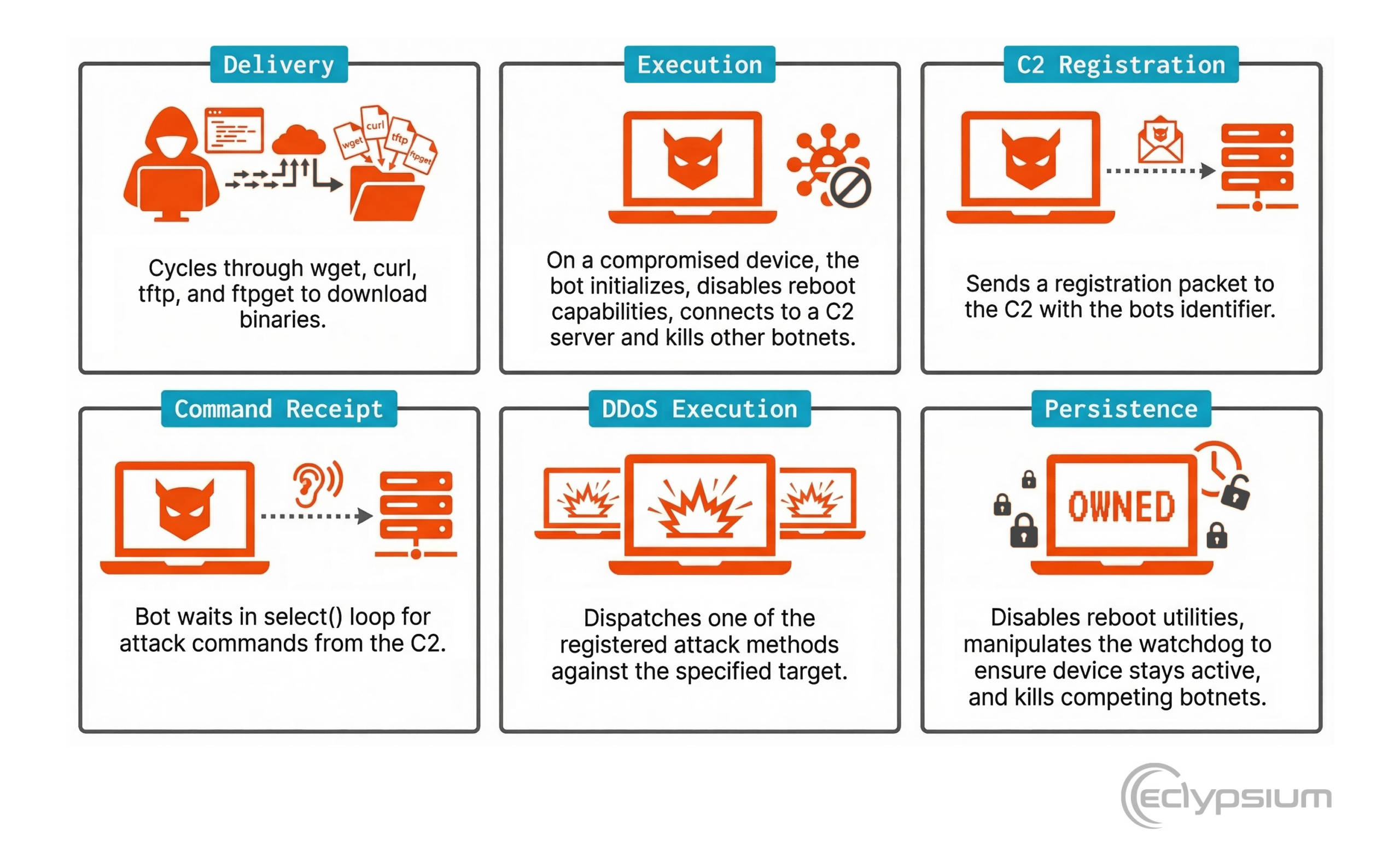
- Delivery: Employs a robust payload drop mechanism that cycles through multiple transfer utilities (wget, curl, tftp, ftpget) to ensure successful download of the multi-architecture binaries.
- Execution: On a compromised device the bot initializes, disables reboot capabilities, connects to a C2 server and kills other botnets
- C2 Registration: Sends a registration packet to the C2 with the bots identifier
- Command Receipt: Waits in select() loop for attack commands from the C2
- DDoS Execution: Dispatches one of the registered attack methods against the specified target
- Persistence: Disables system reboot utilities by setting their permissions to 000, manipulates the hardware watchdog to ensure the device stays active, and kills competing botnets.
Threat Insights
This variant shows some differences with reported Condi samples originally documented by Fortinet in 2023.
- New Unknown Variant – The hashes from the samples were not known to threat intelligence and malware analysis platforms such as VirusTotal, ThreatFox, Hybrid Analysis, and ELF Digest
- Internal identifier – A string extracted from the binary reveals “QTXBOT”. This identifier does not appear in previous reports on Condi and may indicate either a forked variant or an internal project name used by the developers.
- Expanded Attack Surface – This sample registers 32 attack handlers, while earlier condi variants documented fewer modules, the additional handlers likely represent new flood techniques or protocol variants. Seen in FUN_004006c0
- Competitive Botnet Killing – This variant contains process-killing logic that references multiple botnet families. This variant has added an additional botnet to its kill list: /bin/sora.
“Monaco” SSH Scanner & Crypto Miner
“Monaco” is a SSH Scanner + Crypto Miner written in Go 1.24.0 that brute-forces SSH servers across the internet, compromises them, and deploys Monero cryptocurrency miners with the intention of using compromised devices as free compute to generate crypto revenue.
Malware Details
| Malware Family | Cryptominer |
| Filename | executor |
| File Hash | MD5: 3781a533e77c89dfb575d3a94ddf035f SHA-1: 8ac8424de629de2cdc4f76618862d4801c5ff6cc SHA-256: 08e386e9217eac061db97319962523562b292969192bf4505d431a6d087b8057 |
| File Type | ELF 64-bit LSB executable, x86-64, statically linked, stripped |
| Compiler | Go 1.24.0 (gc), built 2025-02-11 |
| Architectural Variants | Compiled for x86-64, ARM32, ARM64, MIPS big/little-endian — targets servers, IoT devices, routers, and Juniper network equipment |
| C2 IP Address | 8.222.206.6 |
| C2 Port | ports 80 (Apache file hosting), 3333 (mining proxy), 12345 (nice C2), 12346 (monaco C2) |
| Mining Pool | gulf.moneroocean.stream:20128 (MoneroOcean) |
| Host indicators | /tmp/monaco or /tmp/nice, chmod 777, XMRig process, MSR writes |
Mechanism of Attack
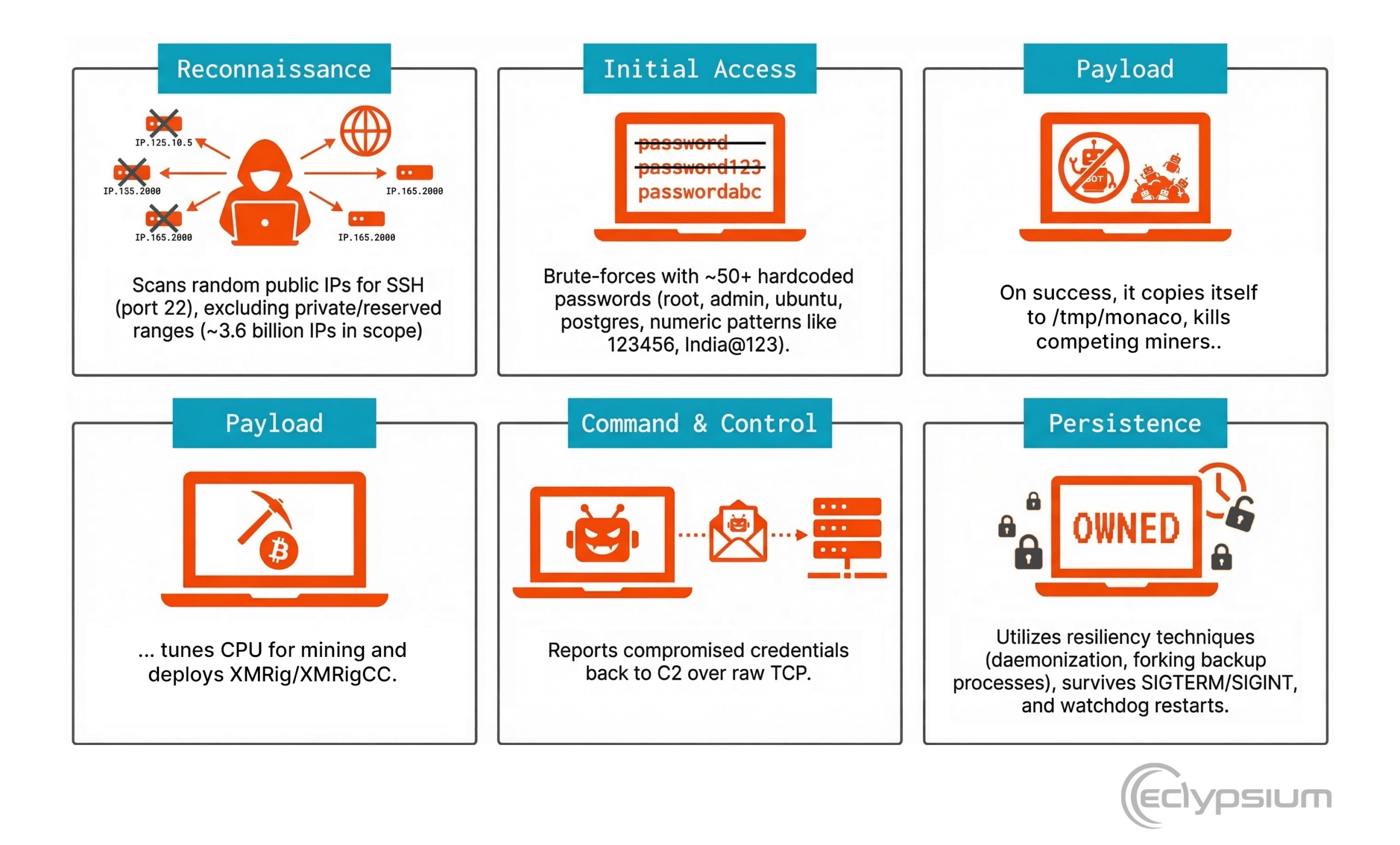
- Reconnaissance – Scans random public IPs for SSH (port 22), excluding private/reserved ranges (~3.6 billion IPs in scope)
- Initial Access – Brute-forces with ~50+ hardcoded passwords (root, admin, ubuntu, postgres, numeric patterns like 123456, India@123)
- Payload – On success it exhibits the following behaviors:
- Copies itself to /tmp/monaco,
- Kills competing miners
- Tunes CPU for mining
- Deploys XMRig/XMRigCC for managing the miners
- Command & Control – Reports compromised credentials back to C2 over raw TCP
- Persistence – Utilizes resiliency techniques such as daemonization, forking backup processes, survives SIGTERM/SIGINT via signal handler, and watchdog restarts after stalled scans
Threat Insights
- Most likely a Chinese-speaking threat actor
- Hosted on Alibaba Cloud Singapore (IP 8.222.206.6, AS45102)
- Alibaba Cloud is predominantly Chinese; CNNIC-allocated AS block; cloud IDE workspace ID pattern consistent with Chinese platforms
- Low sophistication — open directory listing on C2, debug builds left on server, default XMRigCC token mySecret, password skema in plaintext configs
Increasing Trend of Targeting Network Devices
The 2025 Verizon Data Breach Investigation Report found an 8x increase in vulnerability exploitations against network devices. The median time to exploit these was 0 days, where the median time to patch was 30 days. Half of the zero day vulnerabilities exploited in 2025 impacted enterprise technology, with half of those (23% of all zero days) targeting network and security technologies specifically, according to Google Threat Intelligence Group. The Google Cloud Threat Horizons report from H1 2026 indicated that exploitation of third-party software vulnerabilities for initial entry had surpassed weak credentials as a vector for the first time. The trend is escalating.
Threat actors are prioritizing network devices as an initial attack vector due to several unique structural advantages they offer:
- Implicit Trust & “The Visibility Gap”: Most enterprise security stacks (EDR/XDR) are blind to the embedded firmware/software and OS layers of network appliances. Because these devices cannot host traditional security agents, they remain “opaque,” allowing attackers to operate undetected for months.
- Initial Access Without Human Interaction: Unlike phishing, which requires a user to click a link, network devices are often internet-facing by design. Vulnerabilities in VPNs or Gateways allow for zero-click initial access, enabling attackers to bypass the entire perimeter defense in a single move.
- High-Level Persistence: By compromising the firmware of a router or switch, attackers can establish persistence that survives reboots, OS re-imaging, and even hard drive replacements. This “below-the-OS” control allows for long-term espionage and re-infection.
- Strategic Positioning for Lateral Movement: A single compromised switch or firewall provides a pivot point to move laterally across VLANs, bridge IT/OT environments, and intercept or redirect sensitive traffic.
For more technical details about CondiBot and Monaco malware variants, including YARA rules and file hashes, download our complete report.
Tracking the Rise of Network Device Attacks
Eclypsium has been tracking the growth of network-targeting attack behavior for years, and using this information to develop detection and response capabilities against tactics that exploit vulnerabilities EDR and vulnerability management can’t see.
Eclypsium detects persistent implants, backdoors, in-memory malware and anomalous behavior in network edge and core equipment. Eclypsium detects implants and malware used by both Nation-state APTs and ransomware actors. Threat campaigns which used network devices as initial access vector and persistence (A History of Network Device Threats and What Lies Ahead):
- Dec 2025 SonicWall SMA1000: Local Privilege Escalation Used in Zero-Day Attacks
- Oct 2025 F5 Systems Compromised, BIG IP Vulnerabilities Exfiltrated (BRICKSTORM campaign)
- Sep 2025 Surge in Cisco ASA Scanning Hints At Coming Cyberattacks
- Sep 2025 RedNovember attacks Cisco ASA / FTD, Ivanti, SonicWALL, PANW GlobalProtect
- Sep 2025 EOL Devices: Exploits Will Continue Until Security Improves (Cisco, Linksys)
- Aug 2025 Salt Typhoon targets Cisco and Palo Alto network devices (Cisco, Ivanti, PAN, Fortinet, Sophos)
- Jul 2025 Vulnerabilities in Netgear Firmware-Based IoT Devices In The Enterprise
- Jun 2025 The Cisco Vulnerability Salt Typhoon Weaponized Against Canadian Telcos and Viasat
- Mar 2025 Juniper Network Devices Targeted with Custom Backdoors (J-Magic, TinyShell by UNC3886)
- Mar 2025 Silk Typhoon Targeting IT Supply Chains and Ivanti Network Devices
- Mar 2025 Inside Black Basta Ransomware Group
- Jan 2025 PANdora’s Box: Vulnerabilities Found in NGFW
- Nov 2024 Pacific Rim attacks on Sophos Firewall
- Oct 2024 The Rise of Chinese APT Campaigns: Volt Typhoon, Salt Typhoon, Flax Typhoon, and Velvet Ant
- Sept 2024 Velvet Ant attacks Cisco NX-OS and F5 Load Balancers
- Sept 2024 Flax Typhoon with Raptor Train Botnet compromises Citrix andZyxel
- Aug 2024 Fox Kitten Iranian APT Group exploits Citrix Netscaler, Ivanti Pulse VPN, F5, and Palo Alto
- Apr 2024 Arcane Door with Line Dancer and Line Runner implants in Cisco ASA
- Apr 2024 PAN-OS Exploitation leads to exfiltration
- Jan 2024 Volt Typhoon infectsKV Botnet on Cisco, ASUS, D-link, Netgear, and Zyxel routers
- Oct 2023 Citrix attacked byAPT41 (Speculoos backdoor), REvil, Maze ransomware
- Sept 2023 BlackTech APT Group infects Cisco router firmware
- Apr 2023 Jaguar Tooth malware targets Cisco IOS routers
- Nov 2022 Pwned Balancers: Commandeering F5 andCitrix for Persistent Access & C2
- May 2022 F5 BIG-IP exploitation by multiple actors
- Feb 2022 Cyclops Blink malware targets Watchbox Firebox
- May 2021 Ivanti Pulse Secure VPN exploitation by APT5, UNC2630, China-nexus actors, REvil
- Mar 2020 Chinese threat actor APT41 exploits Cisco routers, Citrix, and Zoho
- Aug 2016 SYNful Knock implants backdoors into Cisco ROMMON
What To Do Next
The shift in attack tactics toward exploiting vulnerabilities in network infrastructure requires a shift in defender tooling and mindset. Check out our recent webinar, Firewalls Under Fire: What Breaks Next, And How To Stay Ahead for a step by step walkthrough of how a cyberattack against Fortinet firewalls works to compromise the underlying Linux system and pivot into the rest of the network. We also discuss in detail how to mitigate these risks at Enterprise scale with the Eclypsium Supply Chain Security Platform and other compensating controls.