Netgear (and similar) devices, such as IoT routers, have remained a significant target for vulnerability research and exploitation. This is due to their widespread use in both consumer and enterprise environments, their role as network edge devices, and the persistent challenge of securing firmware and managing patches. With over 500 security advisories released by Netgear, the scale of the problem is undeniable.
Netgear routers and similar devices can pose significant risks in enterprise environments for several reasons:
- Unmonitored and Unpatched: These devices often fall outside traditional patch management and monitoring programs, leaving vulnerabilities unaddressed for extended periods.
- Dual Connectivity: They typically bridge internal networks to the internet, making them ideal for attackers to use as command-and-control (C2) relays or to pivot deeper into the network.
- Supply Chain Complexity: Netgear firmware often incorporates third-party components, increasing the attack surface and the likelihood of inherited vulnerabilities. For example, some devices may use different OS families, such as “Netgear Switch OS”. In contrast, others are based on various underlying systems, making it challenging to apply a one-size-fits-all security approach.
- Use in “Fly Away” Kits: Netgear routers are favored in portable, rapidly deployable network kits for their convenience. However, these kits may be assembled with little regard for firmware security, making them susceptible to compromise and challenging to monitor once deployed.
Netgear’s Commitment To Security
While many cybersecurity practitioners are quick to point out the deluge of vulnerabilities in IoT devices and network and security appliances, Netgear has established itself as a proactive player in the network security landscape. Through its well-documented and mature bug bounty program managed via Bugcrowd, Netgear has become a leader in producing more secure gear than many others. The Bug Bounty program incentivizes security researchers to responsibly disclose vulnerabilities in Netgear’s routers, wireless security cameras, mesh Wi-Fi systems, and associated APIs and mobile applications, offering rewards ranging from $150 to $15,000 depending on the severity and impact of the findings. The program’s rules of engagement and disclosure processes are clear and transparent, helping to foster trust and collaboration between Netgear and the security community. Netgear’s approach is notably more open and structured than that of some competitors, which may lack comprehensive or public-facing vulnerability reporting and reward mechanisms. For example, while other major vendors like Cisco, Fortinet, and Sophos also run bug bounty or responsible disclosure programs, Netgear’s partnership with Bugcrowd and its public commitment to continuous monitoring and rapid patching of vulnerabilities—such as their recent critical RCE fixes for XR and WAX series devices—demonstrate a strong alignment with industry best practices. A recent example was Netgear’s security advisory, PSV-2022-0117, which addressed a critical vulnerability in multiple router models. However, like many in the sector, Netgear still faces challenges with legacy devices, timely patch deployment, and the inherent risks of supply chain complexity. Overall, Netgear’s security posture—bolstered by its bug bounty program—compares favorably to similar vendors and underscores the importance of community engagement and rapid response in today’s threat environment.
CISA KEV Netgear Vulnerabilities
Eight vulnerabilities associated with Netgear products have been added to the CISA KEV, indicating threat actors are actively exploiting these vulnerabilities in the wild. The red color in the chart below indicates that the models affected are currently end-of-service and no longer receive firmware updates.
| CVE Number | Date Added to KEV | CVSS Score | Affected Products | Short Description |
| CVE-2017-6077 | 2022-03-07 | 9.8 | NETGEAR DGN2200 | Remote code execution via crafted HTTP requests. |
| CVE-2016-10174 | 2022-03-25 | 9.8 | NETGEAR WNR2000v5 | Buffer overflow allows remote code execution. |
| CVE-2016-1555 | 2022-03-25 | 9.8 | Multiple NETGEAR WAP Devices | Command injection via unauthenticated web pages. |
| CVE-2017-6862 | 2022-06-08 | 9.8 | Multiple NETGEAR Devices | Remote code execution through HTTP requests. |
| CVE-2017-5521 | 2022-09-08 | 8.8 | Multiple NETGEAR Routers | Authentication bypass allows remote admin access. |
| CVE-2017-6334 | 2022-03-25 | 8.8 | NETGEAR DGN2200 | dnslookup.cgi on NETGEAR DGN2200 devices with firmware through 10.0.0.50 allows remote authenticated users to execute arbitrary OS commands |
| CVE-2016-6277 | 2022-03-07 | 8.8 | NETGEAR Multiple Routers | NETGEAR confirmed multiple routers allow unauthenticated web pages to pass form input directly to the command-line interface, permitting remote code execution. |
| CVE-2020-26919 | 2021-11-03 | 9.8 | Netgear JGS516PE Devices | Netgear JGS516PE devices contain a missing function level access control vulnerability. |
| CVE-2017-7494 | 2023-03-30 | 9.8 | Ready NAS and various routers | Samba Remote Code Execution |
Netgear routers frequently contain outdated software components, such as older versions of web servers (e.g., lighttpd), which may harbor unpatched vulnerabilities. Kernel analysis tools have identified dozens of potential privilege escalation exploits in the Linux kernels used by Netgear devices (e.g., 81 kernel space exploits in one tested firmware).
Threat Research and Attack Trends
- Chinese APT Campaigns: Groups like Volt Typhoon have been observed compromising SOHO routers—including Netgear models—to establish proxy infrastructure for stealthy attacks, data exfiltration, and persistent access to critical infrastructure. These actors leverage exposed management interfaces (HTTP/SSH) and known vulnerabilities to gain a foothold.
- Firmware as an Attack Surface: Attackers and red teams increasingly target firmware due to its lack of monitoring and patching. Network devices like Netgear routers are often overlooked in enterprise security programs, and hundreds of documented vulnerabilities make them attractive for persistence and lateral movement.
- Persistence Techniques: Recent research highlights the use of firmware implants and backdoors that survive firmware upgrades, as well as the modification of integrity-checking binaries to bypass security controls.
- Role in Enterprise and Specialized Kits: Netgear devices are commonly found in branch offices, remote sites, and “fly away” kits—portable network setups used for temporary operations. Their ease of deployment and consumer-grade manageability make them a frequent, if risky, choice in enterprise environments.
How Eclypsium Can Help
As network device threats evolve, so must enterprise defenses. Eclypsium’s upcoming platform release is designed to address the unique challenges posed by devices like Netgear routers:
Vulnerability Identification
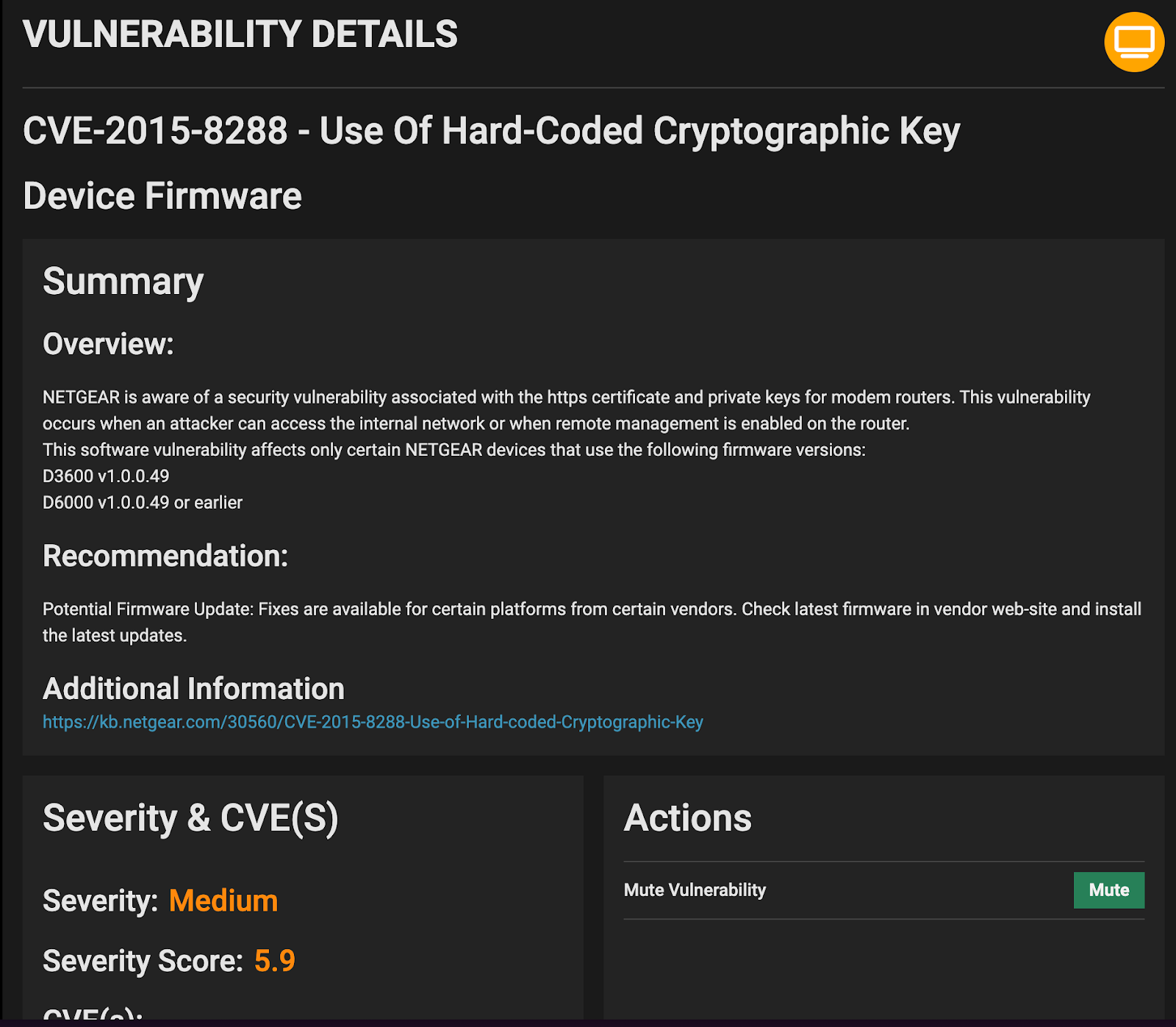
- Automated Firmware Analysis: Eclypsium leverages advanced scanning and analysis engines (including integration with tools like EMBA) to identify known vulnerabilities (CVEs) and risky software components within router firmware, even for devices not directly managed by IT.
- Kernel and Application Vulnerability Detection: The platform correlates firmware binaries and kernel versions with public vulnerability databases, surfacing exploitable flaws such as privilege escalations and web interface bugs.
Firmware Integrity Verification
- Baseline and Monitor Firmware State: Eclypsium establishes a cryptographic baseline of device firmware and continuously monitors for unauthorized changes, including backdoors, implants, and tampering with integrity-checking routines.
- Supply Chain Risk Assessment: By analyzing firmware composition and update provenance, Eclypsium helps organizations detect supply chain risks and ensure only trusted firmware is deployed.
Threat Detection and Response
- Behavioral and Anomaly Detection: The platform detects suspicious activity at the firmware and device level, such as unexpected firmware modifications or the presence of known threat actor TTPs (e.g., persistence mechanisms used by Volt Typhoon).
- Visibility Across All Devices: Eclypsium extends security coverage to unmanaged, “shadow IT,” and specialized kit devices, ensuring that even routers deployed in remote offices or “fly away” kits are included in the organization’s security posture.
Recommendations for Securing Netgear Devices in the Enterprise
- Inventory and Monitor All Network Devices: Include Netgear routers and similar devices in asset management and vulnerability scanning programs to ensure comprehensive network security.
- Apply Firmware Updates Promptly: Regularly check for and apply vendor firmware updates, especially for devices in remote or specialized deployments.
- Restrict Management Interfaces: Disable or restrict remote management interfaces (HTTP/SSH) to trusted networks only.
- Leverage Advanced Firmware Security Tools: Use solutions like Eclypsium to gain visibility into firmware integrity, detect vulnerabilities, and monitor for threats across all network-connected devices.
Conclusion
Netgear routers remain a high-value target for attackers due to their widespread use and the persistent challenge of firmware security. Recent vulnerabilities and threat research underscore the need for comprehensive, automated tools that can analyze, monitor, and protect the firmware layer, particularly as these devices infiltrate every corner of enterprise and field operations. Eclypsium’s platform capabilities deliver the visibility and control organizations need to secure this critical, yet often neglected, attack surface.