Most SaaS products don’t make much noise about version updates and changes. Continuous improvement is, after all, one of the biggest benefits customers receive from an always-improving SaaS delivery model. But every once in a while it’s good to stop and recognize progress towards an encompassing, overarching vision, especially when that vision has the potential to reshape the cybersecurity landscape. That’s certainly the case with version 2.8 of the Eclypsium Platform.
Our Vision
Every device in your enterprise has firmware: from the monitor you might be reading this on to your favorite mobile device and to the servers, routers and gateways that connect us. The average endpoint PC has 15-20 firmware components. The average server has 30 or more. Multiplying firmware components across the number of servers, endpoints and devices, we quickly see that an average enterprise can have hundreds of thousands or millions of firmware components.
Every piece of firmware needs to be protected. Every piece of firmware needs to be assessed for vulnerabilities, regularly updated and monitored for compromise. Yet the security controls we use today — risk-based vulnerability management, endpoint protection, patch and threat intelligence — are all focused on upper layers of the software stack, overlooking this fundamental and massive layer of infrastructure. They are essentially blind to firmware. And of course you can’t protect what you can’t see.
Part 1 of our Eclypsium vision means enterprise breadth. Single platform to secure firmware across your enterprise, whether it’s embedded in a server BMC or in a laptop’s UEFI. For that matter, this single platform should secure firmware in network devices as well as IoT and OT devices and cyber-physical systems like a Siemens Simatic IPC427E. Enterprise breadth means our customers have a consistent way of securing millions of lines of otherwise invisible firmware code across disparate teams and technologies.

Part 2 of our Eclypsium vision means our customers will have unparalleled depth. For every device type we want to provide our customers with a solution that Identifies their devices and the firmware they depend on, Verifies the integrity and secure configuration of that firmware, and where necessary Fortifies that firmware, by updating or patching or securely configuring this otherwise invisible code. “Depth” means we can Identify, Verify and Fortify the firmware through an end-to-end solution.
To be clear, vision isn’t achieved overnight. Nor should it be. “Vision” is big enough and bold enough to guide our long-term strategy and our view of our place in an ever-evolving world. It’s a shared image–a set of ideals–that unites everyone at Eclypsium, from CEO to engineering team to sales and marketing. And it does its unifying work even when meeting notes are lost and priorities run aground or when task lists are nowhere to be found.
Steve Jobs probably said it best:
“If you are working on something exciting that you really care about, you don’t have to be pushed. The vision pulls you.”
The diagram above doesn’t represent the depth of Eclypsium’s capabilities today, but it certainly reflects where we’re going.
Eclypsium for Network Devices is Generally Available
It’s been a tough year for network devices in the cyber-security world.
- Accellion file transfer appliances – in many case twenty-year-old set-and-forget devices – came under intense fire from the UNC2546 UNC2582 cybercrime groups in the form of CLOP ransomware, impacting a swath of organizations like Morgan Stanley, Royal Dutch Shell, and the Reserve Bank of New Zealand.
- This summer, 0-day attacks against Pulse Secure VPNs (see CVEs 2021-22893, 2020-8260 and 2020-8243 for more detail) showed that attackers were enthusiastically focused on network devices and were uncovering new vulnerabilities to exploit.
- This August, CISA re-listed the top exploited vulnerabilities with a surprising twist in year-over-year trends. It’s no longer primarily about defending MS Exchange or applications, but about defending network devices: in 2020, 30% of the top-exploited vulnerabilities were in network devices, but now in 2021 CISA says it’s closer to 69% in network devices.
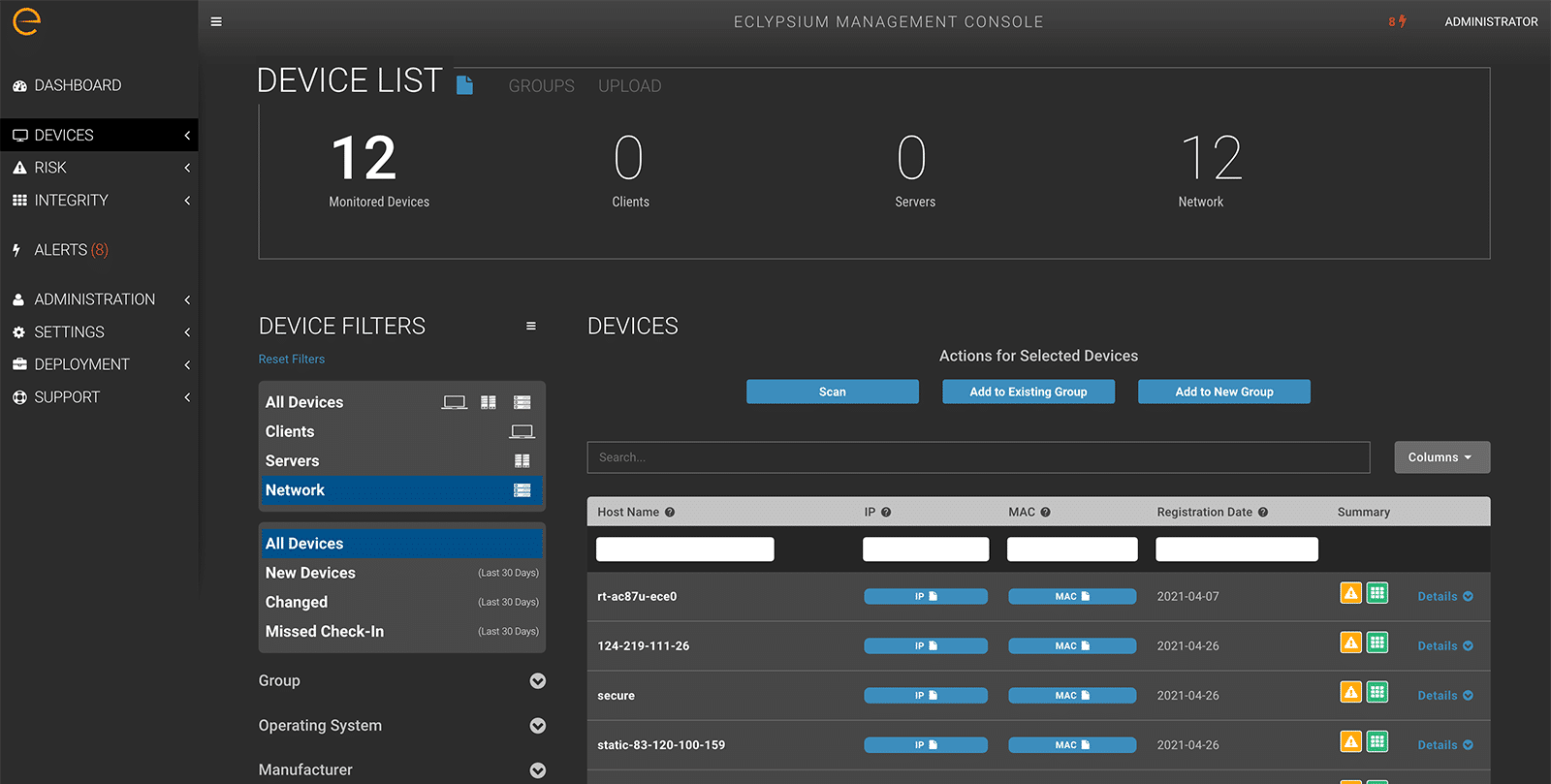
Back in Q2, Eclypsium released the beta version of its Eclypsium for Network Devices product. Now with version 2.8 the “beta” label is gone: customers have tested it and are using it to secure firmware in devices like Cisco, Juniper, Arista, F5, Pulse Secure, Aruba, Fortinet, Accellion, Citrix, NetApp and more.
Eclypsium customers facing a non-stop string of ransomware attacks and intrusion attempts against their network devices can now use the Eclypsium platform to:
- Identify their network devices, like IoT devices, firewalls, routers, and more, even when installed outside of normal procedures or in home offices or in “hidden” network segments
- Verify these devices for required integrity and against known vulnerabilities using the world’s largest database of and firmware profiles, and to a level deeper than any vulnerability assessment can provide
- Fortify network devices by patching and updating as needed, and by prioritizing the threats unpatched and vulnerable devices pose to the organization’s overall security posture
And Eclypsium customers can do this work with the same intuitive, SaaS-based interface (or the same comprehensive APIs, if needed) their enterprise is using to secure the firmware in their endpoints and their servers. What’s more, they can do it wherever their devices are deployed, throughout their far-flung infrastructures or in their hardware supply chains. All of this is a significant step – a leap actually – towards our vision for an end-to-end solution that secures firmware across the entirety of the modern enterprise. Visit the webpage for Eclypsium for Network Devices for more details or to download the product brief.