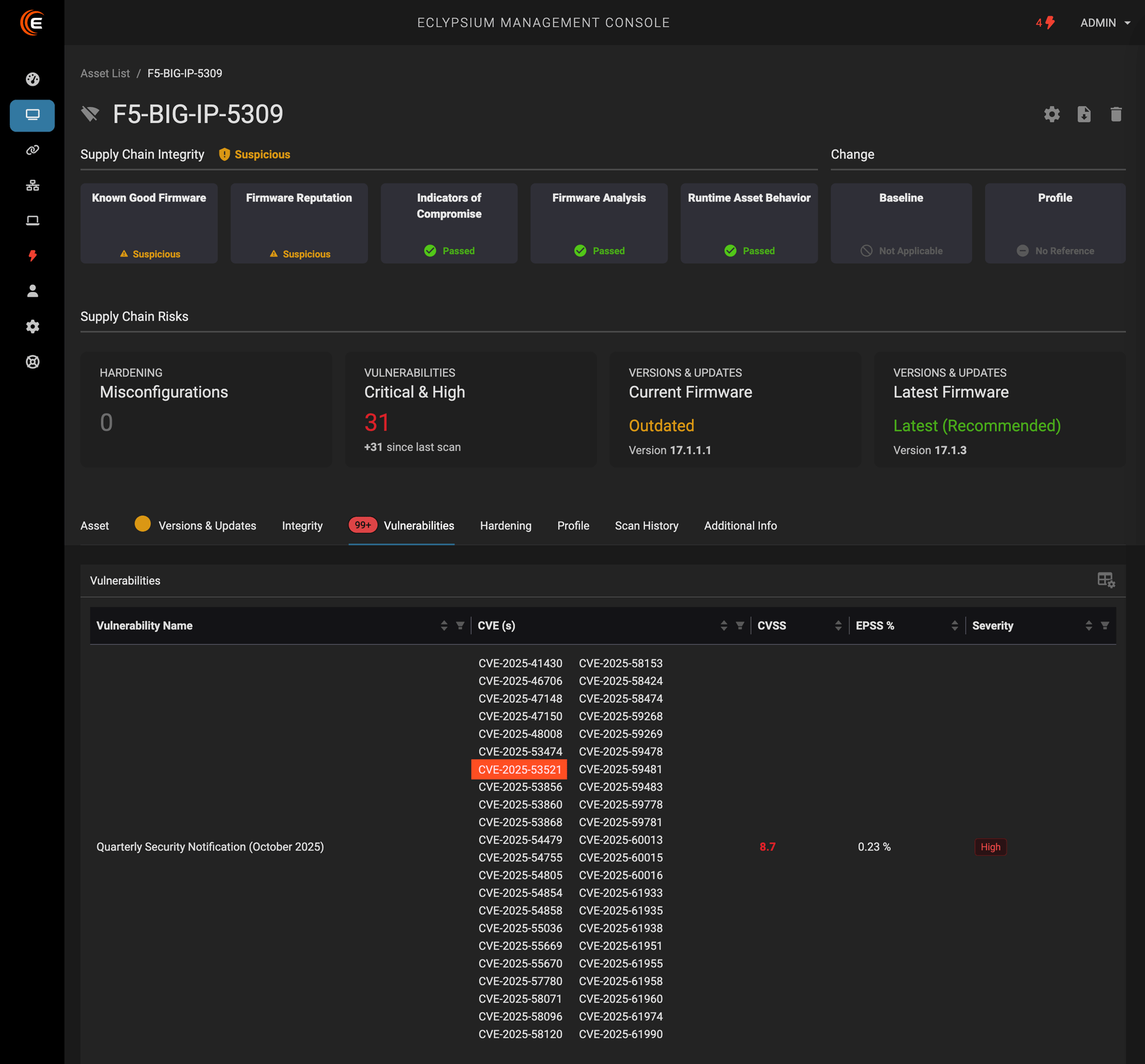
A vulnerability in F5 BIG-IP systems that allows unauthenticated remote code execution by attackers has been added to the CISA Known Exploited Vulnerabilities catalog. CVE-2025-53521 was disclosed on October 15, 2025, but only added to the KEV on March 27, 2026. The vulnerability was originally given a severity score of 7.5, but was adjusted upward to 9.8 when new information emerged in March. The original vulnerability was marked as a Denial of Service vulnerability, but has been updated to indicate that it enables unauthenticated RCE, alongside the disclosure that it is being actively exploited in the wild.
Eclypsium has been able to detect the presence of CVE-2025-53521 since October 16, 2025, one day after the vulnerability’s disclosure.
The Bigger Picture of F5 Vulnerabilities in 2025-2026
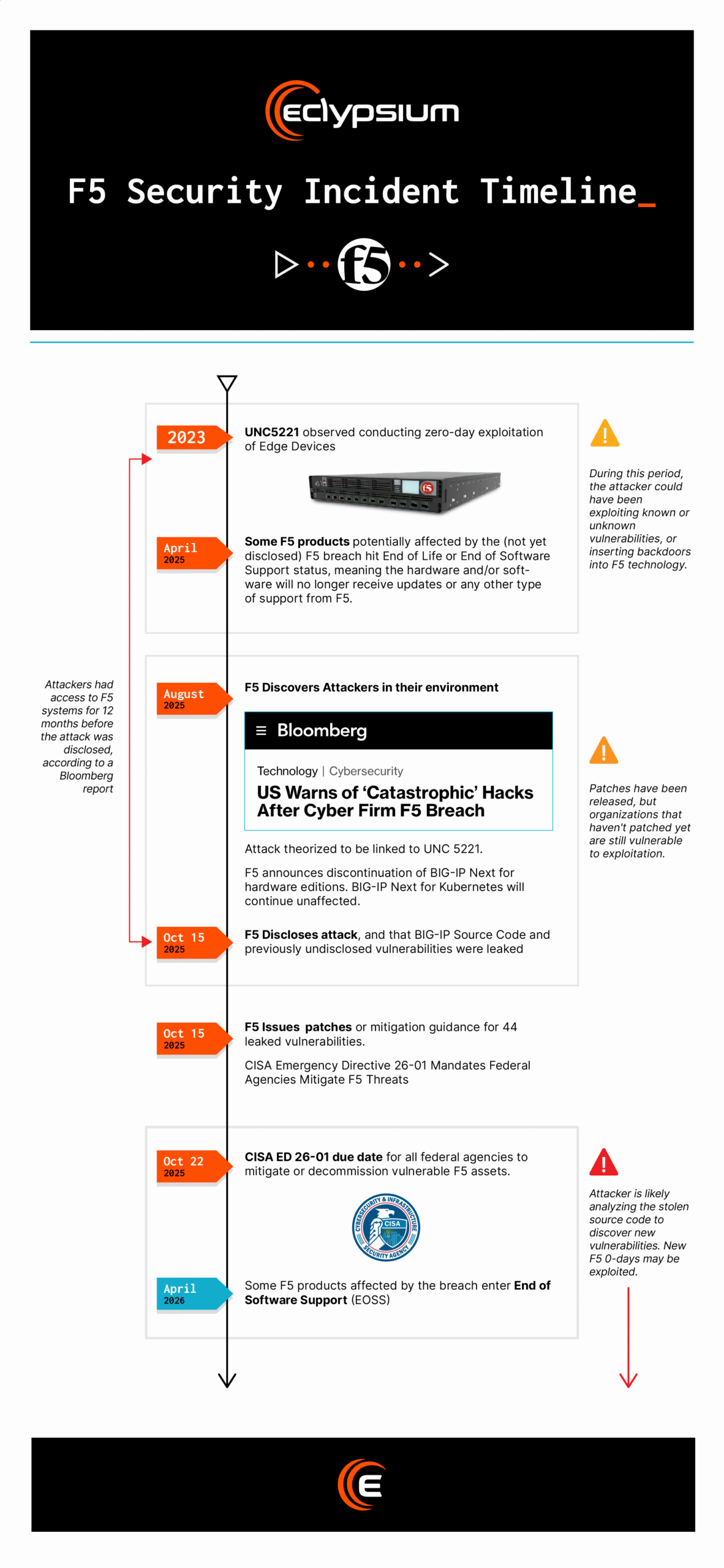
F5 became the focus of intense scrutiny in late 2025 when the company disclosed that hackers had compromised their internal systems, stolen BIG-IP source code, and learned of 45 previously undisclosed vulnerabilities in the F5 BIG-IP platform. The most recently disclosed vulnerability was first disclosed as part of F5’s October 2025 Quarterly Security Notification, published on October 15, the same day they disclosed the breach.
In the wake of this news, Eclypsium customers requested that we do a deep examination of their F5 BIG-IP appliances. The potential for unknown vulnerabilities to be exploited, or new vulnerabilities to be developed against the leaked source code had created a heightened sense of risk inside these organizations. Because of Eclypsium’s deep bench of hardware and firmware researchers, we were able to provide insight into the risk factors still facing F5 hardware inside our customers’ environments. Questions they urgently wanted answers to included:
- Has my organization been impacted by the F5 security incident?
- Can my F5 devices be trusted?
- What are all the F5 devices in my environment?
- What is the current security risk status of my F5 devices?
- What actions can I take to address the risks and threats related to the F5 security incident?
Beyond the individualized reports we provided to customers, we published some of our generalized findings in a report titled The Future of F5 Risk In The Enterprise.
But this incident highlights an unsettling truth that reaches way beyond F5. Network devices in general, from application delivery controllers to firewalls, VPNs, Routers, and Switches all contain code that their end users, major enterprises, worldwide banks, government agencies, and more, are not able to access for monitoring and security purposes.
The Ticking Bomb of Network Edge Risk
2024-2025 saw a 34% increase in vulnerability exploitation for initial access, and an 8x increase in exploits specifically targeting network edge devices, according to the Verizon Data Breach Investigation Report. The top exploited products in Mandiant’s M-trends report were Palo Alto GlobalProtect VPNs. At-Bay cyberinsurance disclosed that their customers with Citrix or Cisco on-premises VPNs were 6.8x more likely to suffer a ransomware attack.
In March, 2026, during a packed RSAC keynote discussion with Pat Opet (Global CISO of JPMorganChase), Pat shared “Don’t Trust the Edge” stats that mirror the ones we’ve been seeing across the threat landscape.
- Top 4 most frequently exploited vulnerabilities were on edge devices
- 8x increase in edge device exploitation YOY
- 50% of critical vulnerabilities fixed were on edge devices
He also said, “At JPMC, we regard patches as exploits…The moment a patch is published we are already running out of time…Edge devices are a target because of our inability to instrument those devices to get visibility.”
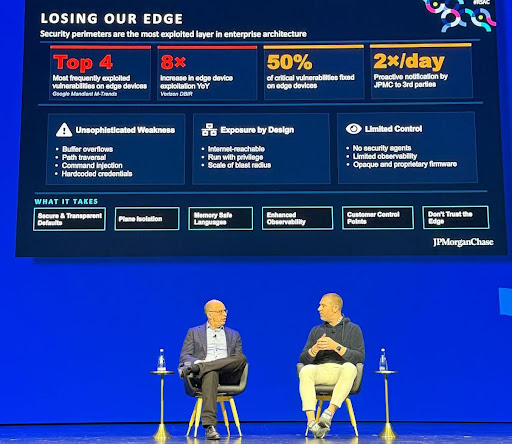
When one of the world’s largest banks talks about network edge risk this way, it signals that now is the time to start taking it seriously. In the past, nation state attacks like the F5 breach could be dismissed as unlikely to affect the majority of businesses due to their cost and sophistication. These attacks are no longer reserved for the most advanced threat actors. They affect the IT hardware supply chain of security products, intended to protect, which have become the stomping grounds of cyber adversaries, from APTs to ransomware gangs.
As Opet hinted, firewalls, VPNs and more are harder to monitor than endpoints because you can’t install endpoint agents on them. And when half of network edge vulnerabilities are exploited before being disclosed, traditional vulnerability management is rendered ineffective.
The best way forward is to start monitoring the underlying systems, the operating system and firmware that sit beneath these widespread platforms.
Eclypsium Can Help
Eclypsium automatically scans F5 devices and other network edge infrastructure to provide a detailed firmware bill of materials, providing a more comprehensive asset inventory to use in risk analysis, attack surface management, and incident response. Eclypsium also detects known vulnerabilities and indicators of compromise on F5 devices, as well as products from Cisco, Palo Alto, Citrix, Fortinet, Arista, Juniper, and many others, making it much harder for cyber adversaries to hide their activity and live off the land inside critical network infrastructure.
To learn more about rising attacks targeting network edge devices and IT infrastructure, check out our ebook: Eradicate Hidden Risks in Network Edge Devices: Critical Insights for Security Leaders
Frequently Asked Questions
CVE-2025-53521 is a critical vulnerability in F5 BIG-IP systems that allows unauthenticated remote code execution. It was originally disclosed in October 2025 and classified as a denial-of-service vulnerability with a severity score of 7.5, but was revised upward to 9.8 after new information surfaced that it enables full unauthenticated RCE. CISA added it to the Known Exploited Vulnerabilities catalog in March 2026, confirming active exploitation in the wild. Eclypsium was able to detect its presence beginning October 16, 2025, one day after initial disclosure.
F5 disclosed that a nation-state actor accessed a proprietary BIG-IP development network, including source code and details about vulnerabilities still under development. The actor involved was UNC5221, a China-based state-sponsored group known for stealing source code from major tech providers, linked via Mandiant to the “Brickstorm” malware. In response, CISA released Emergency Directive 26-01, mandating that federal agencies inventory and patch all BIG-IP hardware, as well as all instances of BIG-IP F5OS, BIG-IP TMOS, Virtual Edition, BIG-IP Next, BIG-IQ software, and BNK/CNF, with end-of-service BIG-IP devices required to be decommissioned.
Not entirely. While patches have been released for the 44 vulnerabilities across numerous F5 products that were leaked to attackers during the breach, some vulnerabilities in BIG-IP Next that were stolen during the incident have not been patched. There’s also an open question about what comes next: the potential for unknown vulnerabilities to be disclosed in the future must be factored into every enterprise’s assessment of whether to trust F5 devices.
In August — the same month F5 discovered the presence of attackers in their environment — they announced the discontinuation of BIG-IP NEXT. The BIG-IP NEXT project had been positioned as a more agile replacement to the “monolithic” TMOS operating system underlying many F5 products. Some elements of BIG-IP Next have been scrapped, including those applying to hardware and virtual editions, while BIG-IP Next for Kubernetes will continue development unaffected. You can read more in Eclypsium’s full analysis of future F5 risk in the enterprise.
It’s much broader. The Verizon DBIR Report for 2025 noted an 8x increase in exploitation of vulnerabilities against network edge devices. Earlier in 2025, the U.S. National Guard revealed that their networks had been compromised by Salt Typhoon via their Cisco and Palo Alto Networks equipment. CISA also issued Emergency Directive 25-03 focused on widely deployed Cisco ASA appliances. F5 is one chapter in a much longer story about the systematic targeting of network infrastructure. For a deeper look at the trend, see Eclypsium’s coverage of the F5 incident in context.
Network edge devices like firewalls, VPNs, routers, and load balancers run custom firmware and integrated operating systems that fall outside the reach of standard endpoint detection and response (EDR) tools and conventional vulnerability scanners. You can’t install an endpoint agent on a firewall. That visibility gap is exactly what sophisticated attackers exploit to gain access, establish persistence, and move laterally — often undetected for extended periods.
Yes. Eclypsium Research discovered and reported severe remotely exploitable vulnerabilities in F5’s Next Central Manager that could grant attackers full administrative control, allowing them to create hidden accounts on any F5 assets it manages — accounts that would not be visible from the Central Manager itself. Eclypsium has also tracked F5 exploitation going back to CVE-2022-1388, where attacks were first detected on Eclypsium honeypot devices just five days after the CVE was publicly disclosed.
The immediate priorities are inventory, patching, and integrity monitoring. Organizations should know every F5 device in their environment, the firmware version it’s running, and whether it’s past end-of-support. For those with dozens or hundreds of BIG-IP appliances deployed, the specter of undisclosed vulnerabilities having fallen into attackers’ hands requires urgent incident response. Beyond patching, compensating controls — including continuous firmware-level monitoring — are essential, since patching alone can’t account for vulnerabilities that haven’t been disclosed yet. Download Eclypsium’s guide to eradicating hidden risks in network edge devices to learn more.