Cheating has been around since the beginning of electronic gaming, dating back as far as 1981. Players have always wanted to use shortcuts or aids as an advantage to clear the game faster or gain an advantage over other players. Yet, despite the evolution of “gaming cheats,” the motivation has always remained the same – people just like to do things the easy way – and without getting caught.
Since the humble days of the Commodore 64, gaming has grown into a multi-billion dollar industry with mega brand names and live broadcasts of eSports events. These events have become so mainstream that it has become common to see online betting and gambling on eSports tournaments and events.
Additionally, online gaming has evolved to a whole new business model in recent years based on in-game micro-transactions. In this model, players are given the option to purchase in-game items or exclusive in-game access rights using real-world dollars. “World of Warcraft” is a classic example, where players could spend a lot of time collecting and mining for resources, or they could simply purchase game currency with real money. This led to a whole industry of “gold miners.” This allowed game developers to establish ongoing revenue streams in which players are initially allowed to play for free. However, microtransactions have subsequently spread to all types of games as well.
And as gaming has become more competitive and in-game features more valuable, the value of cheating has grown as well. This has made anti-cheating its own business and spawned a back-and-forth “war” between cheat creators and game developers. Over the years, the industry has seen iterative advancements in offensive and defensive techniques from either side of the “trenches.”
The Connection to Computer Security
As both sides have progressed, game cheat developers are forced to find new and creative ways to hide their code from anti-cheat engines. In fact, the anti-cheat engines in some games are more complex and powerful than the protections such as antivirus used to protect more traditional applications. This is because games have more rigorous requirements. Any manipulation of game data such as modifying player stats, health, or inventory can fundamentally change the game.
Oddly enough, the high privileges and deep access to the operating system has made these anti-cheat engines a target for attackers. Just in the past few weeks, researchers have uncovered ransomware operators using vulnerable anti-cheat drivers from the popular game, Genshin Impact. In this case, the attackers were able to use the anti-cheat drivers in order to disable antivirus services on a compromised host.
It’s also been well-known for years that the cheating community is often at the forefront of security by discovering bypasses and new exploitation techniques well before they are published as a cybersecurity threat or concern. Furthermore, gaming cheats bring plenty of reward with a fraction of the risk. Gaming cheats can be both highly profitable without carrying the same level of risk compared to more offensive security scenarios such as using malware. Simply put, there is plenty of money in gaming, and it is substantially more legal than cybercrime.
Another interesting trait of cheats is that the cheater is often hacking their own device. With multiplayer games, there are two main classes of devices that can be targeted by hackers; the server which runs the game and coordinates between all of the clients and the clients themselves. Some types of cheats may require hacking the server, but that’s generally more difficult and likely better protected than the client software itself. If the goal is to win, there’s a lot of benefit for the player to target their own computer which is running the client software. Because the player is typically the valid owner of the client device, they will often have the privileges to disable various security controls. Unlike a traditional malware threat, which often needs to escalate privileges without being seen by a user, cheaters typically have full control over their devices. And in on-line, multiplayer games, important data is often delivered to the client where a cheating player can easily manipulate it. In order to decrease the amount of game lag due to network traffic and server-side processing, games will often send data to the client that shouldn’t be displayed to the player. This can provide an advantage to players who can view or otherwise take advantage of that secret information that other players don’t have access to.
Cheats Take the Fight Below the Operating System
In the gaming world, cheaters are mostly known as “hackers”, a moniker given to those who “use hacks” rather than those who actually do the “hacking.” In the cybersecurity world, “hackers” are the ones creating and using the hacks, and the ones simply using tools are known as “script kiddies” or “skids”.
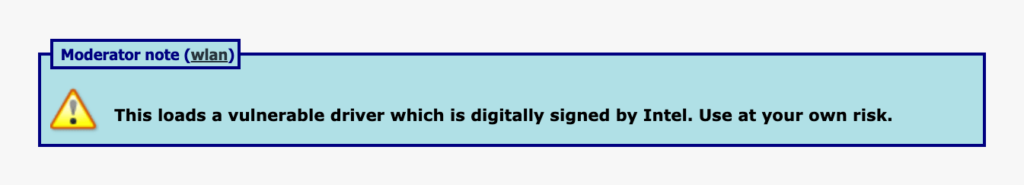
But regardless of the terminology, cheaters are constantly trying to outsmart the operating system. This makes sense since the OS is responsible for running both the game and any anti-cheating technologies. One common technique is for cheating tools to utilize a known vulnerable windows driver in order to get read and write access to game memory and modify it. For example, the three-year-old kdmapper driver takes advantage of a vulnerable Intel driver. The vulnerable iqvw64e.sys driver is included with Intel LAN drivers and provides the ability to copy, read and write user/kernel memory, map physical memory and perform virtual to physical address translation. In order to gain actual code execution, we can use the method described here for executing shellcode.
And this is where things get even more interesting. Since the goal is to read and modify data while avoiding protections, we have seen an increase in gaming cheats that go below the OS and use UEFI firmware as their base of operation. Since the firmware is more privileged than the operating system, some creative developers and researchers have created ways to introduce a bypass in the system before the operating system loads, such as ways to spoof hardware IDs. This can allow cheaters to avoid being banned if they are caught simply by spoofing certain hard-to-fake hardware characteristics in order to trick the game into allowing them to create a new account on the same banned computer.
These UEFI-based tools/cheats would allow a computer’s owner to alter the boot process flow by introducing these tools in the middle of the process. Normally Secure Boot is designed to prevent such manipulations of the boot process, but since the “attacker” in this case is the computer owner/user, they can simply turn Secure Boot off and run the code.
In recent years, game developers have increasingly sought to ensure that client devices are properly using various protections and security features. For example, developers increasingly check that Secure Boot is enabled and that the system has a Trusted Platform Module (TPM) before the game can be played. This, in turn, created the need for a new kind of cheat capable of making it appear that Secure Boot is properly enabled even when it is not. And once again, since the goal is to lie to the operating system, the UEFI proved the ideal place to fake the presence of Secure Boot.
Where We Go From Here
This leads to an incredibly interesting intersection of gaming and cybersecurity. Malicious hackers, from the most advanced state-based adversaries to the most common malware and ransomware groups, have already turned to UEFI and firmware as a way to subvert a system’s operating system and security controls. Firmware and security below the OS is a truly deep topic and an active area of research. If you would like to learn more, we encourage you to check out some of the latest research on the Eclypsium blog.
Gaming cheats have been doing many of the same things as attackers and for many the same reasons. However, the cheating scenario actually poses some unique challenges because the “attacker” is also the valid user/owner of the system. Instead of trying to keep external attackers from wresting control of the boot process and pre-OS code execution, anti-cheating technologies will have to do so when the “attacker” is fully and legally in control of the device itself.
It also creates the potential for cross-pollination between gaming cheaters and cyber threats. Will cheaters lead the way by discovering new security bypass techniques? On the other hand, will cheaters dip into the malware arsenal and use exploits and techniques as a lower-risk use of malicious code? One thing is certain – this will be a fascinating area to keep tabs on going forward.