The FCC recently announced a ban on the sale of consumer-grade internet routers manufactured outside the United States. More specifically, the FCC received a National Security Determination that caused them to update their “Covered List,” to include all foreign-made consumer-grade routers.
The stated purpose of the ban is to reduce cyber risk against American consumers. But several details of the ban, and the process for manufacturers to get an exception for their products, have raised serious doubts about whether it can achieve the intended goal, or whether it might even have the opposite effect.
First, the definition of a “consumer-grade router” cited in the FCC Public Notice implicitly only includes devices actually marketed as routers, as well as their supporting phone apps and backend infrastructure. But it does not pertain to the wide range of other smart, networked devices that are manufactured abroad and are increasingly prevalent in American households. Routers are only a small subset of the devices we all have at home that contain the hardware and software necessary to route packets and can be co-opted into an adversary’s botnet.
Additionally, the ban applies only to consumer-grade routers that the FCC has not already approved for import and sale in the U.S. That means the existing routers in American homes that cyberattackers have already compromised can continue to operate.
On top of that, the subsequently published guidelines for obtaining conditional exceptions to this ban focus heavily on localizing manufacturing in the U.S., implying that the cyber risks being addressed stem from the international supply chain for routers.
In reality, the security issues in consumer routers are less a result of where they’re manufactured, and more driven by lax attention to security in the firmware, software, and management interfaces of these devices. While foreign adversaries certainly could introduce security flaws into these routers during their manufacturing, they mostly don’t need to try that hard. The types of vulnerabilities present in these systems are widespread and prevalent even in currently up-to-date models. Older, end-of-life models that no longer receive software and firmware updates are even more riddled with security holes.
Bob Rudis, a lecturer at Carnegie Mellon University, put it perfectly in his own excellent writeup:
“Moving router assembly to a factory in Texas does not fix a buffer overflow in the web management interface. It does not patch a hardcoded credential in the firmware. It does not address the fact that millions of consumers never update their router software and most router vendors abandon security updates for older models within a couple of years.“
In our own previous discussions of this topic, one of the most surprisingly controversial issues surrounded what actually counts as a router or not. The closer you look, the less obvious it is, and the less clear it is that this ban will mitigate any cyber risk at all.
Our Most Surprising Viral Controversy: What Is (Or Can Be) A Router?
Cyber risk introduced via the IT device supply chain is a topic of great interest to Eclypsium. But we almost didn’t write about the router ban because it has already been covered so heavily in the tech and cybersecurity press. But then we interviewed an industry veteran who stopped by our booth at RSA 2026 and posted a 49 second clip from that interview on YouTube and it blew up!
In the clip, Josh Marpet (friend of Eclypsium and occasional guest on our Below The Surface podcast), suggested that devices like smart TVs could be considered routers, based on the presence of WiFi hardware, RJ45 connections, and the underlying software. The YouTube commentariat had OPINIONS about this. The clip quickly racked up over 450,000 views, 5,000 likes, and over 500 comments, many of which were debating the specific claim that a TV is a router.
Here’s the clip:
Given the fervid debate in the YouTube comments about what actually counts as a router, we thought it would be interesting to dig into the specific language of the FCC’s public notice and the documents it cites to triangulate which devices and vendors are actually affected, and how this will affect the cyber risk posture of American consumers.
How The FCC Defines A Consumer-Grade Router
The FCC’s Public Notice about the router ban references NIST IR 8425 A which defines a consumer-grade router as something that routes packets between networked devices, and can be installed by the consumer. Their specific phrasing of the definition is:
“A “consumer-grade router” is a router intended for residential use and can be installed by the customer. Routers forward data packets, most commonly Internet Protocol (IP) packets, between networked systems.”
This definition is tautological, implying that only devices marketed as routers are included in the ban. The NIST IR document also includes third party applications and backend services that support the router, as illustrated here.
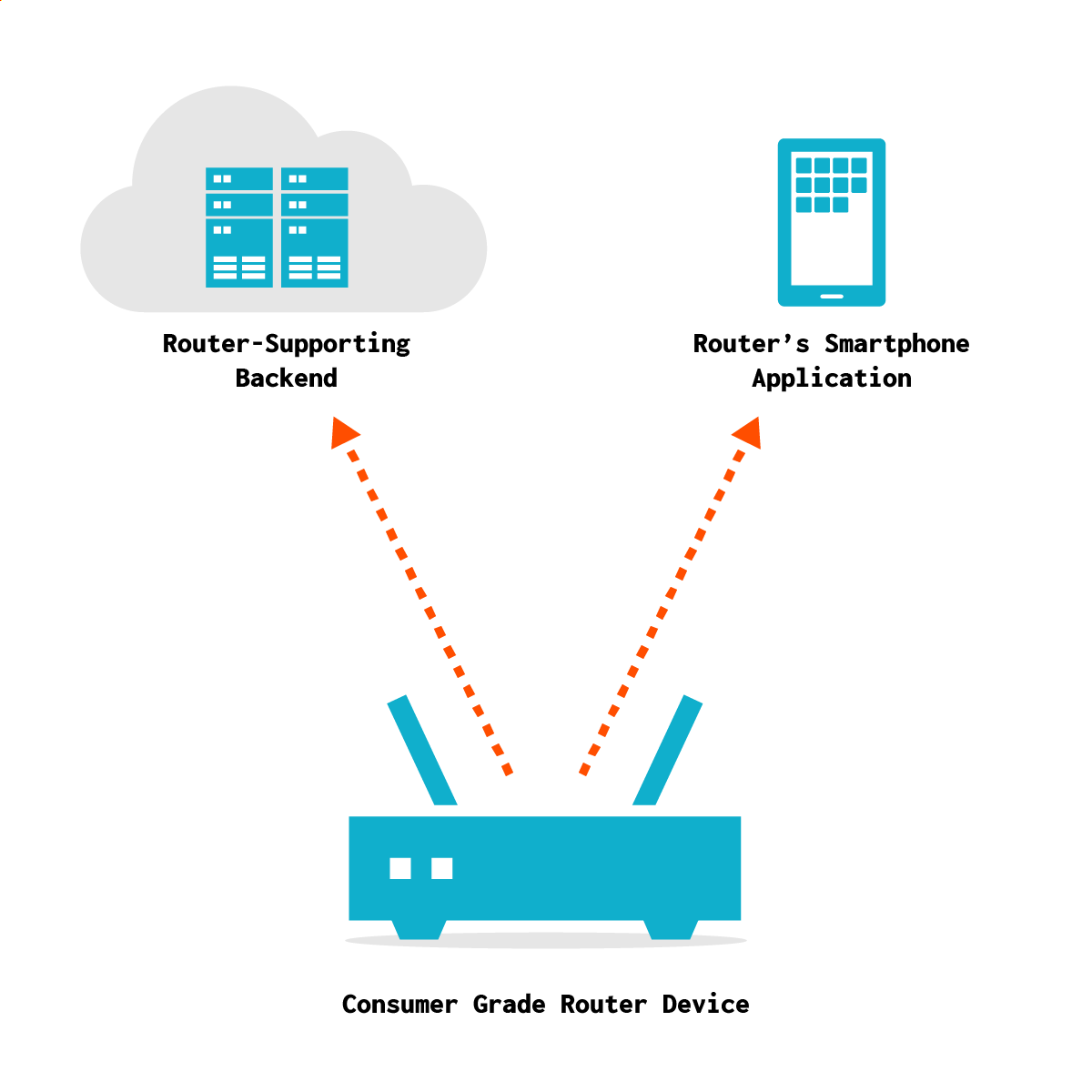
Source: NIST IR 8425-A
So the FCC probably didn’t intend to include all home devices that have the hardware and software to be able to act as a router in this ban. Their intent was to ban devices marketed as routers to consumers. Going even further, the ban only applies to new devices. Models that have already been approved are still allowed to be imported and sold. You can still use the router you bought last year at your house.
Furthermore, devices that are marketed as routers are only a subset of the large universe of devices that can be trivially compromised and made to act as routers for the purpose of nation state botnets. Notably, the Flax Typhoon APT built out a botnet comprising SOHO routers, IOT devices, and NVR/DVR devices, proving that the risks from these threat actors extend well beyond the “consumer-grade routers” that are banned by the new FCC rule.
This doesn’t take into account the other devices that can be compromised and re-configured to act as routers, which includes essentially every home computer, smartphones, and other gadgets.
Going even further, there’s a robust DIY culture and toolset around building your own router from component parts and open source software. Turns out, people hate the garbage combined modem-routers their ISPs lease out to them. Plenty of people take it into their own hands to build a nicer router out of cheap x86 computers, WiFi cards, and other readily available components. That won’t be the largest percentage of Americans, but it is yet another illustration of the gaps in this overly broad, yet somehow still gap-riddled FCC ban.
This is not to say SOHO routers face zero cyber risk. They do! And some of that risk is introduced through their hardware supply chain. But the notion that banning devices marketed as routers to consumers will meaningfully reduce cyber risk to United States critical infrastructure demands closer scrutiny.
What Is The Role of Consumer Routers In Nation State Cyberattacks?
A National Security Determination like this router ban can be made either through congress or by the Executive Branch. In this case, the Executive Branch interagency body issued a document highlighting recent major cyber attacks targeting vulnerable small-office and home-office (SOHO) routers to “carry out direct attacks against American civilians in their homes” as the reason for banning routers made abroad.
The determination cited Volt Typhoon, Flax Typhoon, and Salt Typhoon, three major attack campaigns that targeted critical infrastructure in the U.S. and elsewhere in recent years, and which are still operating today, as examples of the types of attacks that will be stymied by the ban. The central premise of the router ban is that foreign-manufactured SOHO routers create cyber risk against Americans. But if critical infrastructure is the primary target, what role do SOHO routers play, and how will banning them mitigate the risks?
Salt Typhoon, Volt Typhoon, and Flax Typhoon, all high-profile APT campaigns associated with the People’s Republic of China, did involve SOHO routers to some degree. The primary way that consumer-grade SOHO routers are involved in these and other nation-state attacks is as an intermediate proxy infrastructure that the adversary can use to obfuscate the source of their actions and launch attempts to compromise enterprise servers and networks inside their actual targets: critical infrastructure organizations.
Furthermore, all of the threat actors named in the FCC document also targeted enterprise network devices, many of which are deployed with known vulnerabilities inside critical infrastructure organizations from power companies to telcos to Federal government agencies.
In fact, in 2025, enterprise network edge devices like Palo Alto Global Connect and VPNs from Cisco and Citrix were the most targeted devices according to the Mandiant mTrends report and At-Bay Cyberinsurance company. The cyberinsurer noted that organizations with on-premises VPNs from certain vendors were 6.8x more likely to suffer ransomware.
2025 also saw numerous CISA Executive Directives and Binding Operational Directives requiring government agencies to rapidly decommission enterprise network gear that had been found to have actively exploited vulnerabilities in it.
“End Of Life” Devices Are The Most At Risk
When it comes to targeting either SOHO or enterprise network infrastructure, the most at-risk devices are those that are “end of support” or “end of life” and have stopped receiving software and firmware updates from their manufacturers. Volt Typhoon specifically targeted end-of-life Netgear and Cisco devices. Earlier in 2026, CISA Binding Operational Directive 26-02 focused explicitly on the risk represented by end of life devices.
This is a critical factor in examining the FCC router ban because of a detail in a subsequent document released by the FCC, describing a “waiver of prohibitions on certain class I permissive changes to covered routers.” The document says that even pre-approved routers are only guaranteed to be allowed to receive new software and firmware updates until March of 2027. After that, router manufacturers that have not received an exception to the new controls may not be allowed to distribute software updates.
If new updates are forbidden starting in March of 2027, it would effectively render all routers from companies that haven’t received an exception to “end of life” status at once. Given that end of life devices still operating on outdated firmware are a primary target for cyberattackers, this seems to undermine the potential effectiveness of the ban in achieving its stated goals.
How Do You Get A “Conditional Exception?”
The FCC has published more details on the pathway for vendors to apply for what it calls a “Conditional Approval.” In practice, this is the only way a company can keep selling affected devices in the U.S. under the new rules.
The application process reads less like a certification and more like a full supply chain disclosure. Vendors are expected to provide detailed information about ownership, including foreign stakeholders, as well as a comprehensive breakdown of their manufacturing, design, and development processes. That includes where firmware is written, where hardware is assembled, and who is involved at each stage.
On top of that, companies are asked to outline plans for shifting production into the United States over time. The implication is pretty clear: approval is not just about proving current security, but about demonstrating a trajectory toward domestic manufacturing.
Notably, the FCC isn’t the entity making the final call. Submissions are evaluated by national security agencies like DHS and the Department of Defense, which assess whether a given product poses an “unacceptable risk.” Approval, if granted, is temporary and can be revoked.
So while there is technically a path to exemption, it’s narrow, opaque, and heavily tied to broader geopolitical and supply chain considerations, not just the security properties of the device itself.
Stepping back, the FCC router ban raises more questions than it answers. The definition of what counts as a router is narrow and somewhat arbitrary, while the underlying cyber risks it aims to address extend far beyond that category. Without clearer alignment between the policy and how these attacks actually work, it’s hard to see how much security benefit this rule will ultimately deliver.
For a deeper dive on the technical possibility of turning nearly any home computing device, including a Smart TV, into a router, and how that impacts American cybersecurity, go watch our Below The Surface podcast episode about this (featuring Josh Marpet from the viral clip)!






