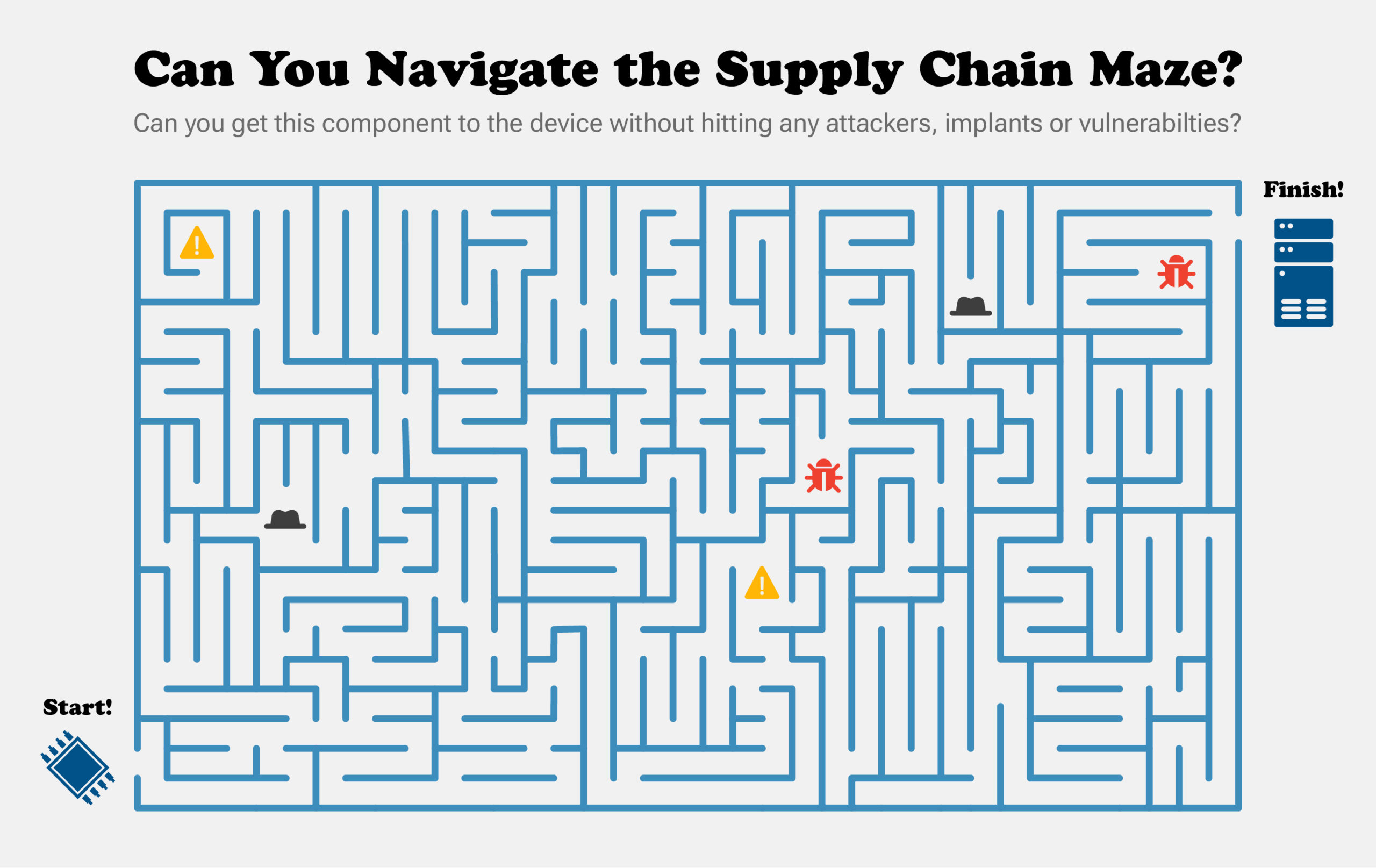
Supply chain security is one of the most pressing challenges for security leaders today. Organizations naturally rely on their technology, and virtually all of it is the result of highly complex and increasingly turbulent supply chains. A mistake or compromise at any of the dozens of suppliers, sub-suppliers, OEMs, distributors, and resellers can give an attacker virtually unlimited control of an asset long before it is ever delivered to the customer.
Supply chain risks and threats also pose a variety of unique challenges that can hit organizations where their defenses are typically the weakest. From the attacker’s perspective, this is all very much by design. For example, by targeting the supply chain, attackers are effectively shifting the battle to a time and place before enterprise defenses are present. An adversary can target an upstream supplier with lax security, or state-based adversaries may even be able to infiltrate or coerce an in-country supplier. In either case, many of the initial steps of the cyberattack will take place far away from the eventual customer’s defenses. In addition to fighting earlier, supply chain attacks also let adversaries take the fight below the layers that traditional security tools work. Infiltrating the supply chain can give attackers access to the most privileged inner workings of an asset, such as the underlying firmware that controls how a device boots or how a physical component actually works below the level of the operating system.
These changes have major impacts on what is required from security tools. While the high-level goals of finding vulnerabilities and threats remain the same, how that actually gets done is very different when it comes to the supply chain. Let’s take a look at a few examples of how this new class of risk requires a new class of security tool.
A Master Mechanic for Your Devices
When technology works well, we rarely have to give it much thought. We flip a switch, the light comes on, and we don’t need to think about the hundreds of little details that made that possible. IT assets take this concept to an extreme and do so by design. Each layer of technology is designed so that it is abstracted from the layer below it. This is true for everything from the OSI model of networking to virtualization to the physical operation of a server appliance.
The problem is that in order to audit the supply chain, we actually need to know exactly how all the various pieces work together. We need to know how every low-level component and setting in an entire device is supposed to work together in order to find problems. It’s a bit like being a master mechanic for every type of device. We probably don’t want to strip a server down to bare-metal and rebuild it piece by piece, but we DO have to know how it all works in order to see when something is wrong.
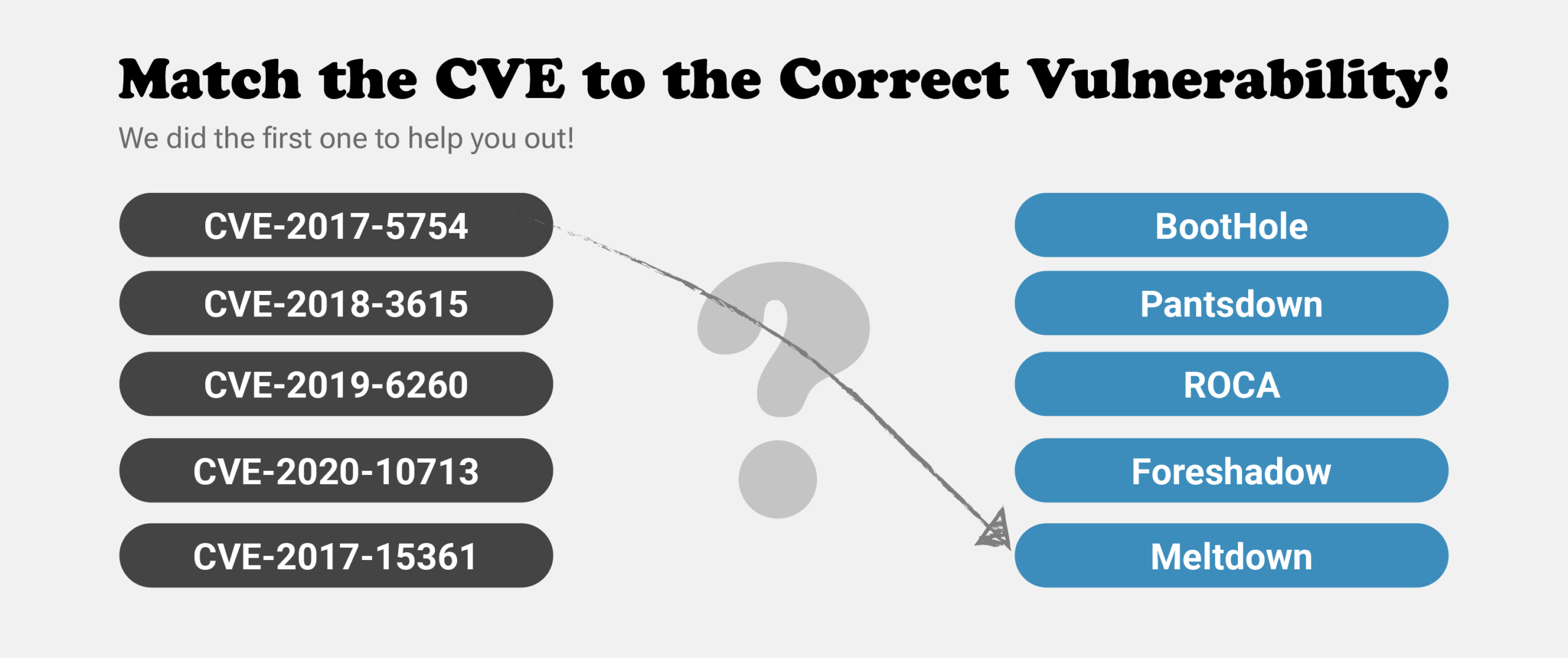
And this is where AV, EDR, and vulnerability scanners completely fall apart in terms of supply chain security. AV and EDR tools view the world in terms of malicious binaries or, at best, the indicators of a threat. Their focus is overwhelming on the level of the operating system and will occasionally look down into system firmware. However, they are not at all designed to audit the dozens to hundreds of components, protocols, and settings that need to work together. The same is true for vulnerability scanners – they may know individual CVEs, but not how devices actually work.
The same challenges apply even to the built-in protections found in many modern systems. Secure Boot is a standard part of many systems, but our repeated research into malicious bootloaders has illustrated how small problems in the extended supply chain can render Secure Boot powerless. Oddly enough, this problem gets even more complex as the built-in security in devices gets stronger. For example, Secured-core PCs rely on a carefully coordinated combination of protections working together, including Secure Boot, System Management Mode (SMM), Trusted Platform Module (TPM), Dynamic Root of Trust for Measurement (DRTM), Memory Access Protection, Hypervisor Code Integrity (HVCI), and more. Each element can have its own vulnerabilities, and if they aren’t all working together properly, then the whole system can fall apart.
A supply chain security platform, on the other hand, is purpose-built to understand this complexity. And it repeats this knowledge across a wide range of assets such as laptops, servers, networking gear, IoT devices, and more. This enables Security and IT teams to quickly and automatically audit a device to ensure that everything under the hood is working properly and nothing is amiss either due to a mistake or an intentional act in the supply chain.
Library of Good
Traditional security tools are designed to look for bad things such as malware, exploits, or indicators of compromise. At a high level, they seek to map the world of what is “bad”. We do the same thing in supply chain security, although the threats can be very different (more on that shortly).
However, supply chain security also requires that we map the world of what is “good.” Unlike more traditional software, the physical components and the firmware that drives them actually remain quite predictable. This means that it is at least possible to build a massive, industry-wide catalog of firmware and hardware. This makes it possible to quickly scan an asset and confirm that every piece and component is running the code that it is supposed to. Any deviations from the known good firmware can immediately reveal a loss of integrity in the supply chain.
Eclypsium has by far the industry’s largest library of firmware profiles. The Eclypsium database includes over 6 million elements from over 200,000 update packages, covering more than 95,000 distinct devices that include a vast range of vendors, device types, and models. Eclypsium is constantly expanding and maintaining this database as vendors roll out new firmware.
This ability to look for the good also extends to the behavior of components and firmware. Once again, the behavior of individual components and firmware will remain remarkably consistent over time. This means that a supply chain security platform can quickly identify any unusual behaviors in a component even if the code itself seems to be valid. This is particularly important in supply chain security since attackers can potentially insert malicious code in valid, properly signed vendor code, as seen in the Sunburst attacks.
Fighting Below the OS (BtOS)
We have already seen how it is important to see down into the most fundamental layers of a device in order to detect supply chain risks and threats. However, this is not a trivial task and another area where most standard security tools come up short. Even for the purposes of scanning for vulnerabilities, tools will need very specialized drivers in order to get to the lowest level code on a device.
Even more importantly, most security tools rely on the operating system itself in order to query down to the hardware and firmware layers of a device. This creates a circular problem because one of the whole reasons that attackers go below the OS is so that they can subvert and deceive it. For example, the recent iLOBleed highlighted the ability of malicious firmware to prevent staff from updating firmware, yet falsely reporting that the firmware was successfully updated. Device components also can contain their own independent communication stacks as seen by the PLATINUM group’s use of Intel AMT as an OS-independent command-and-control channel and attacks against server BMCs.
Supply chain security tools will use a variety of mechanisms to see the same information, including using OS-independent methods. This enables the tools to find any alterations even when attackers attempt to evade security.
Key Take-Aways
These points have really just scratched the surface of what it takes in order to do supply chain security well. But hopefully, this starts to map out some of what makes supply chain security platforms truly unique and how they can bring new insights into your security practice.
In short, if you want to find a piece of malware, then you need to have deep insight into binaries and executables. If you want to secure a supply chain, then you must have a much larger perspective. You must know what is supposed to be in each element of the supply chain and be able to recognize when a product or component has been altered. You must understand how the many components and technologies come together to work as a whole and if there are weaknesses or misconfigurations that could undermine the posture of the device. You must be able to dive to the lowest levels of detail in a device and independently verify the integrity of each piece and component. The good news is that a platform such as Eclypsium can do these things automatically. So as new vulnerabilities are discovered, or a vendor swaps out one supplier for a cheaper, less secure alternative, or an advanced adversary drops an implant into a firmware update, an organization’s IT and Security teams can find the problem proactively. To learn more, please contact the Eclypsium team at [email protected].






