CISA’s Advisory On Botnets: Why Banning SOHO Routers Won’t Fix Critical Infrastructure Cyber Risk

CISA recently released a new cybersecurity advisory focused on defending against botnets built from compromised consumer and small-office/home-office (SOHO) routers. The advisory highlights how threat actors are actively exploiting vulnerable, internet-exposed devices to build large-scale proxy networks.
The timing of CISA’s advisory is notable. It arrives shortly after the FCC’s controversial move to restrict the import and sale of certain foreign-made consumer routers. Taken together, the message is clear: the SOHO router supply chain is being framed as a meaningful source of cyber risk to U.S. critical infrastructure.
There’s truth in that. But it’s also only part of the picture.
If the goal is to reduce cyber risk to critical infrastructure, focusing primarily on consumer routers risks missing where the most impactful leverage actually lies. It is in defending the enterprise edge of critical infrastructure companies.
Why SOHO Router Botnets Matter
SOHO routers have become a convenient resource for nation-state threat actors, including China-nexus groups such as Volt Typhoon, Flax Typhoon (Raptor Train), Salt Typhoon and others.
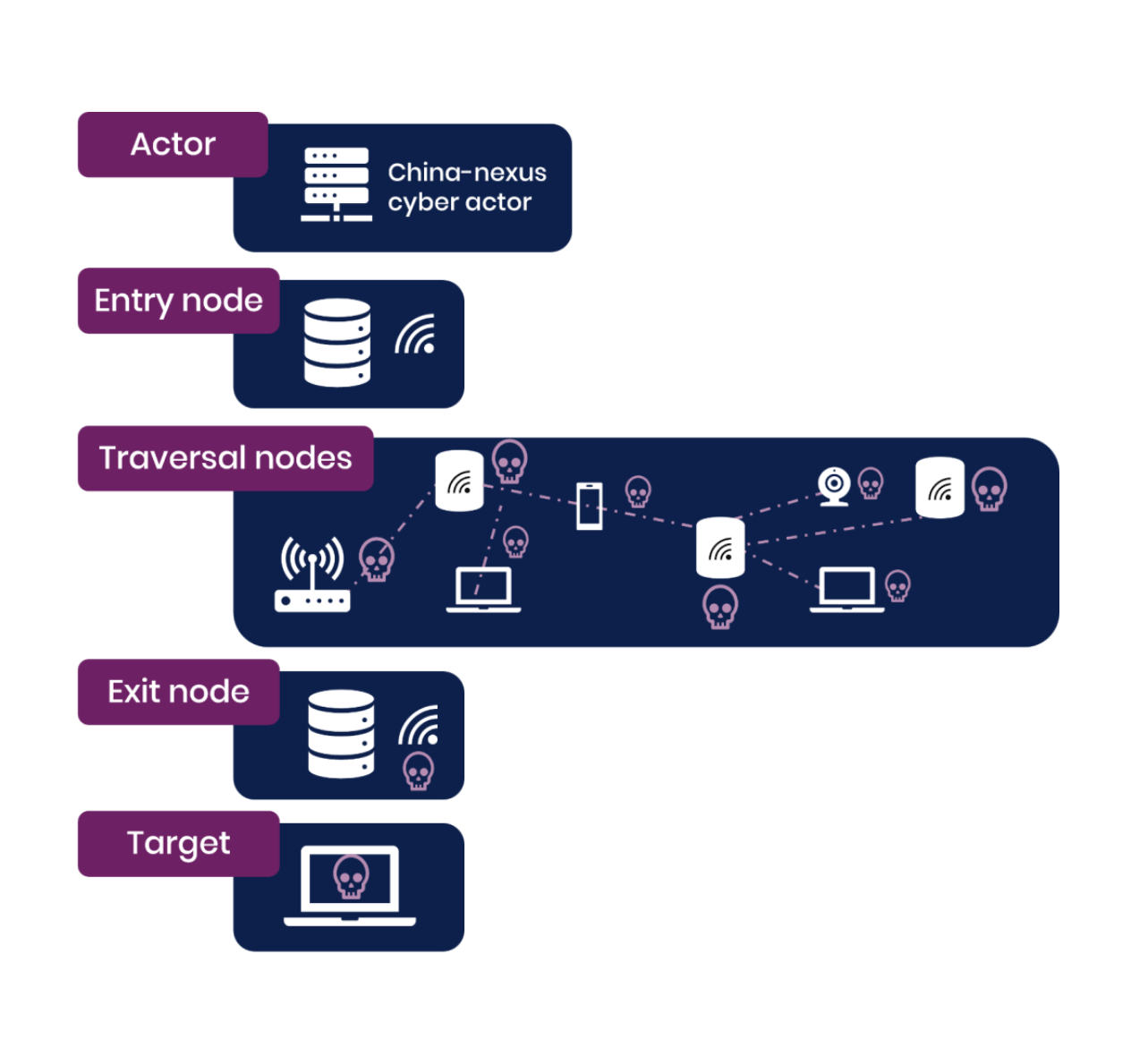
The model is straightforward:
- Exploit unpatched or poorly secured routers
- Maintain persistence on those devices
- Use them as distributed proxy infrastructure
This gives attackers several advantages:
- Anonymity: Traffic appears to originate from residential IP space
- Resilience: Takedown is difficult due to scale and geographic distribution
- Plausible deniability: Attribution becomes significantly more complex
These botnets are not a target in themselves, but a staging ground. From there, attackers launch campaigns against higher-value environments including telecommunications providers, energy systems, and other elements of critical infrastructure.
Mitigating this class of threat is absolutely worthwhile. Restricting high-risk devices from entering the market may reduce future exposure at the margins. But it doesn’t address the full problem.
What the CISA Advisory Actually Recommends
Beyond highlighting the threat, the advisory also provides concrete guidance for organizations to defend against this activity. The recommendations include:
- Mapping and understanding network edge devices, with a clear inventory of what assets exist and what should be connecting to them
- Establishing baselines for normal network behavior, particularly around VPNs and remote access services
- Identifying anomalous connections, including traffic originating from consumer broadband ranges
- Leveraging dynamic threat intelligence feeds to identify known malicious infrastructure
- Implementing multifactor authentication for remote access
None of this guidance is controversial. In fact, it reflects well-established security best practices.
And that’s the point.
These are not new controls introduced in response to SOHO router botnets. They are foundational measures that organizations responsible for critical infrastructure should already have in place.
The Real Implication of the Guidance
Taken at face value, the advisory is framed around external risk driven by botnets built from compromised consumer devices. But the defensive measures it emphasizes are almost entirely focused on internal visibility and control.
- Knowing what devices exist at the network edge
- Understanding what “normal” looks like
- Detecting deviations from that baseline
- Securing access pathways like VPNs
This is not about stopping botnets from being created. Organizations don’t control that. Protecting the organization comes down to the condition and integrity of the systems inside the network.
If enterprise edge devices are properly secured, patched, monitored, and validated, then it matters far less whether an attacker is routing traffic through a compromised home router or any other proxy infrastructure. You can worry a lot less about getting targeted by botnets if they’ve got nowhere to actually break in or pivot inside your own network.
Where Organizations Actually Have Leverage
There’s a tendency to focus on upstream threats. But most organizations can’t effectively act on information about where attacks originate, what infrastructure adversaries are using, or how they build scale.
For defenders, the highest leverage is almost always downstream. Organizations cannot realistically prevent botnets from being created. They cannot control the global population of vulnerable consumer devices.
What they can control is their own environment:
- Whether their network infrastructure is running vulnerable or end-of-life firmware
- Whether their devices are authentic and free from supply chain tampering
- Whether access paths are hardened with strong authentication
- Whether abnormal activity is detectable and acted upon quickly
That’s where the outcome of an attack is decided.
The Limits of a Consumer Router Ban
Banning or restricting certain SOHO routers may help, but it’s an incomplete solution for several reasons.
First, the existing installed base of vulnerable devices doesn’t disappear. Millions of routers already deployed across homes and small businesses will remain exposed for years.
Second, attackers are adaptable. If one class of device becomes harder to exploit, they will shift to others. The Mirai botnet was recently discovered targeting DVR devices. The same potential lies within countless consumer and enterprise IOT devices, edge appliances, or any system with weak security controls and internet exposure.
Third, enforcement is inherently uneven. Grey markets, resale channels, and secondary distribution paths make it difficult to fully control what devices are actually in use.
In other words, a router ban can reduce some risk at the edges. It does not fundamentally change the attacker playbook.
The Bigger Risk Is Already Inside Critical Infrastructure Networks
If we step back and look at where these campaigns are ultimately headed, a more uncomfortable reality emerges.
Critical infrastructure organizations and federal agencies already operate large amounts of vulnerable network technology inside their own environments.
This includes:
- Firewalls with known, actively exploited vulnerabilities
- VPN appliances exposed to the internet
- Routers and switches running outdated or end-of-life firmware
- Network management interfaces accessible from untrusted networks
CISA has issued multiple executive directives, advisories and binding operational directives over the past year calling for the remediation or removal of exactly these types of systems.
The pattern is consistent: attackers don’t just rely on external infrastructure like SOHO botnets. They actively target weaknesses within enterprise networks themselves.
In many cases, these systems are:
- Directly exposed to the internet
- Highly privileged within the network
- Difficult to patch or replace quickly
From a risk perspective, that combination is far more consequential than a compromised consumer router acting as a proxy.
Supply Chain Risk Doesn’t Stop at Consumer Devices
The focus on foreign-made SOHO routers also highlights a broader concern about supply chain risk. The concern is valid, but the current supply chain is so complex and international that achieving a U.S. only supply chain for technology products will take years or decades. That isn’t a solution for immediate risk. And again, the risk being addressed in the router ban is not confined, or even primarily relevant to consumer hardware.
Enterprise and mission-critical systems face significant supply chain challenges of their own, including the persistent issue of counterfeit components.
A 2019 report from the Defense Systems Information Analysis Center estimated that approximately 15% of spare and replacement parts for U.S. Department of Defense equipment are counterfeit.
Counterfeiting affects a wide range of technologies:
- Network switches
- Graphics and compute hardware
- Embedded systems used in defense and infrastructure
The risks associated with counterfeit or unauthorized components go beyond reliability:
- Modified or malicious firmware
- Hidden backdoors
- Inconsistent or unpatchable software states
Unlike a vulnerable consumer router on the edge of the internet, these components are often deployed directly within sensitive environments. That makes their potential impact significantly greater.
The Real Gap is Lack of Device Integrity Visibility
Across both consumer and enterprise contexts, one theme keeps emerging: organizations often lack visibility into the actual state of the devices they depend on.
Security decisions are frequently based on assumptions:
- That hardware is genuine, and has been provided in a secure state by the vendor
- That firmware is up to date and hasn’t been tampered with
- That configurations match expected baselines
Those assumptions are not always verified before deploying the hardware.
This creates a gap between what organizations believe about their infrastructure and what is actually true. That gap is where supply chain risk lives.
The Need For Continuous Device Integrity Validation
If the objective is to meaningfully reduce cyber risk to critical infrastructure, the focus needs to shift from restricting specific device categories to verifying the integrity of all devices in use.
That means treating device trust as something that must be continuously reëstablished, not assumed.
A more effective model includes integrity checks and security validation across the entire device lifecycle:
Before deployment:
- Validate hardware authenticity
- Verify firmware integrity against known-good baselines
- Confirm supply chain provenance
During operation:
- Continuously monitor for firmware drift or unauthorized changes
- Detect configuration anomalies
- Identify unexpected behavior at the device level
Throughout the lifecycle:
- Ensure patch integrity, not just patch presence
- Track end-of-life status and enforce replacement policies
- Revalidate devices after maintenance or component changes
This approach directly addresses the root issue: whether the devices inside critical infrastructure can be trusted.
Policy vs. Practice
Efforts like the FCC router ban are not without merit. They signal recognition that supply chain risk is real and that hardware can be an attack vector. But policy interventions alone cannot solve a problem that is fundamentally technical and operational.
Attackers are not limited to one class of device, one vendor, or one supply chain path. They exploit whatever is available, wherever verification is weakest.
If defensive strategies focus too narrowly on restricting inputs by controlling what can be bought or imported, they risk overlooking the much larger challenge of securing what is already deployed.
Where the Real Leverage Lies
SOHO router botnets are a real threat, and mitigating them is worthwhile. However they are a means to an end.
The actual targets remain critical infrastructure networks, where vulnerable, unverified, and sometimes counterfeit systems already operate with high levels of access and trust.
If we want to reduce risk in a meaningful way, the focus needs to move closer to those environments. Not just controlling what enters the supply chain, but continuously validating what is already inside the organization’s walls.
Security isn’t determined by where a device was manufactured. Routers made in America will still have vulnerabilities, and will still reach end-of-support with units in the wild operating outdated firmware. It’s more effective to focus on whether you can trust what your devices are doing right now.
The Full Network Edge Risk Landscape
The landscape of risk at the network’s edge reaches far beyond SOHO router botnets. Our recent webcast untangles the growing risk facing enterprises from their own firewalls, VPNs, routers, and switches, with professional analysis of the F5 source code leak, recent Cisco Firepower exploitation, and more. View our webcast: Edge Of Catastrophe: How Network Device Attacks Became The Biggest Cyber Battleground.
FAQ: CISA Botnet Advisory and FCC Router Ban
CISA’s advisory focuses on the growing use of compromised consumer and SOHO (small-office/home-office) routers to build large-scale botnets. These botnets act as proxy networks that attackers use to obscure their origin and launch attacks against higher-value targets such as critical infrastructure systems.
Attackers exploit unpatched or poorly secured routers to create distributed infrastructure that provides anonymity (traffic appears residential), resilience (hard to take down at scale), and plausible deniability (difficult attribution). These botnets are not the end goal—they are staging platforms for attacks on enterprise and critical infrastructure networks.
Only marginally. A router ban may reduce some future exposure, but it does not address the large existing base of vulnerable devices already deployed, attackers’ ability to pivot to other device types (such as IoT or DVRs), or inconsistent enforcement across global supply chains. It does not fundamentally change attacker behavior or risk outcomes.
CISA emphasizes foundational security practices at the enterprise edge, including maintaining an accurate inventory of network edge devices, establishing baselines for normal network behavior, detecting anomalous connections (such as traffic from residential IP ranges), using threat intelligence to identify malicious infrastructure, and enforcing multifactor authentication for remote access. These measures focus on internal visibility and control rather than stopping botnets themselves.
Organizations should focus on securing and validating their own infrastructure. This includes patching and monitoring enterprise edge devices like VPNs and firewalls, verifying hardware authenticity and firmware integrity, detecting abnormal device behavior and configuration drift, and continuously validating device trust throughout its lifecycle. Risk is driven more by weaknesses inside the network than by the external botnets used to reach it.