“All you really need to know for the moment is that the universe is a lot more complicated than you might think, even if you start from a position of thinking it’s pretty damn complicated in the first place.”
- Hitchhiker’s Guide to the Galaxy by Douglas Adams
The Universe of Digital Supply Chain
Imagine you are offered a drink. You don’t know what it is or what’s in it. It’s unlikely you’d drink it unless you trust the person giving it to you or some third-party attesting that its contents are safe to drink, perhaps through some certification label with ingredients listed. Yet this type of blind trust is exactly what we do when it comes to the external technology, both hardware and software, we use in our organizations.
Every modern organization depends on products from hundreds of vendors and suppliers. In the age of global interconnected digital supply chains, every product is built using components from many other suppliers, from software and hardware vendors to open-source developer communities.
Software supply chain security or more generally digital supply chain security is an important topic of conversations. Software is everywhere—from every application, to every device and its components. Fundamentally, we can view the entire digital supply chain security space as having two distinct and complementary parts: application software supply chain security and infrastructure supply chain security.
The application software supply chain security part helps software developers and vendors protect their software development environment and applications they build which typically includes source code analysis, analysis of third-party and open-source dependencies, and securing the CI/CD and delivery pipelines. For an overview of solutions focusing on the developer side of software supply chain security, I recommend reading Software Supply Chain Vendor Landscape research.
In this post I will focus on the other part of the digital supply chain security landscape: Infrastructure Supply Chain Security, or solutions which help organizations secure the supply chain of external products they use in their IT infrastructure.
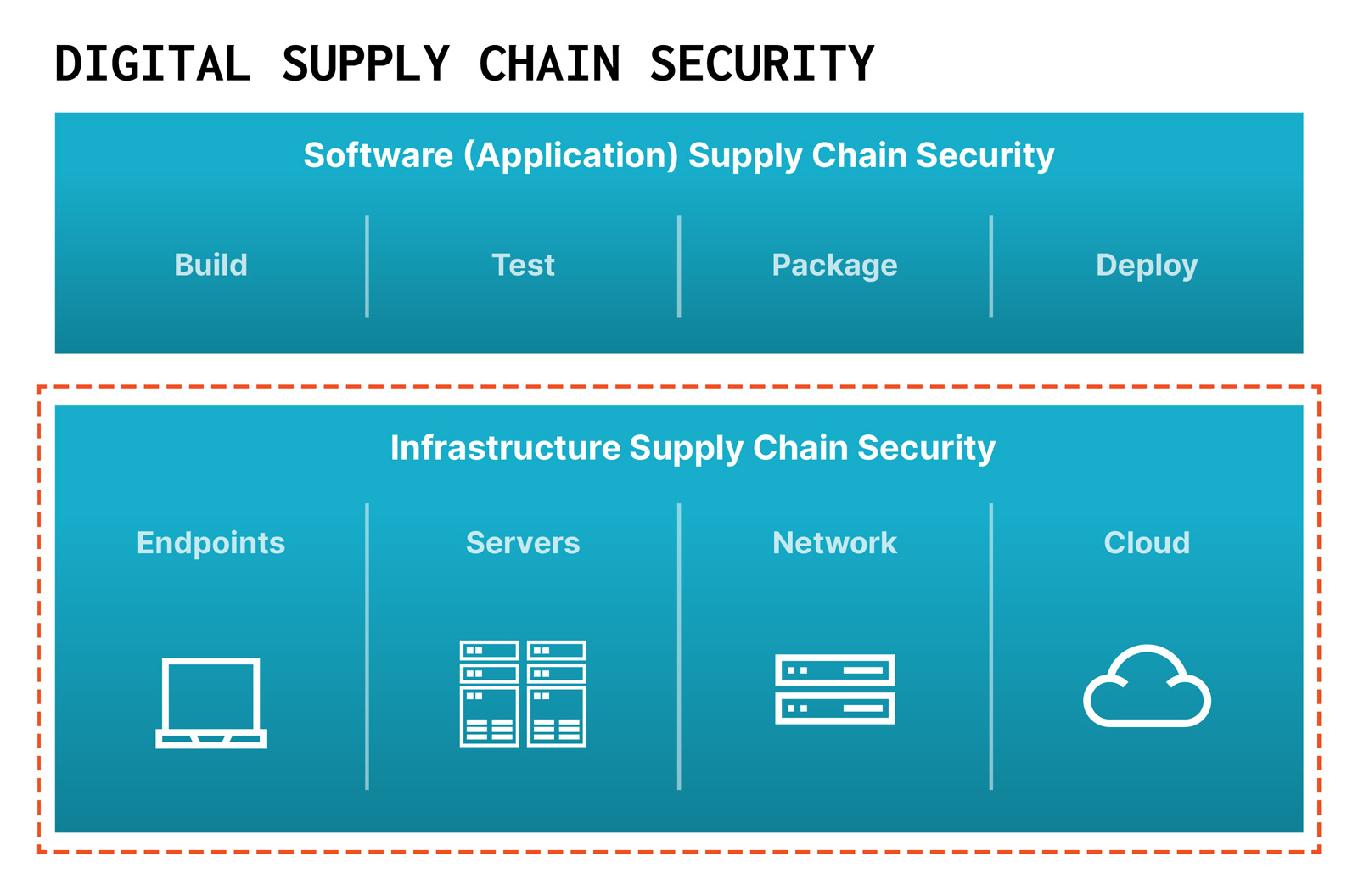
Enterprise IT infrastructure combines multiple types of products such as user devices (endpoints), servers in corporate IT and data centers, network devices in network infrastructure, the software and hardware stack powering cloud infrastructure, and other types of infrastructure which are rapidly developing like enterprise IoT.
Infrastructure is what runs critical applications and workloads and is therefore fundamental to their security. If the infrastructure is vulnerable or compromised, all applications and workloads handling sensitive data are impacted.
Let me start with a simple example.
A typical PC is built by 65 direct suppliers, with another 200 upstream suppliers based in 39 countries who build the components and develop the underlying code. A popular HP Pavilion 550 desktop has over 4,500 models with various configurations of components and versions of motherboards. Each Pavilion 550 has multiple components from CPU to graphics cards to network adapters to storage devices to management chips—each of these components runs their own software or firmware code, from Linux-based OSes to equally complex firmware architectures like UEFI to proprietary code developed by suppliers of these components or their third-party suppliers.
The Modern “Cybersecurity” Problem Is a Supply Chain Security Problem
Do we want to trust all of our vendors and all of their suppliers? Are we confident that each one of them will build secure software and hardware according to the security practices our organizations require? Have any of our suppliers been compromised by threat actors? These components could be altered or have backdoors, introduced by suppliers or external threat actors. All of these components have security vulnerabilities which are going to be used to compromise organizations using these products.
This is just one example: a PC such as the one you might be using to read this article. The problem grows exponentially larger when you consider other parts of your IT infrastructure, such as servers running critical workloads, network devices, and software technologies powering cloud infrastructure. Every time we blindly trust these products and components from the outside, we are accepting a substantial amount of risk.
A server may have anywhere between 50 and 100 of these components. A network device from Cisco, F5 Networks, HPE Aruba, or other vendors are similarly complex systems running their own network OS. Components like the Apache Log4J software library are used by both software applications and network devices, and thus were impacted by the Log4Shell vulnerability. As I write this, organizations across the globe are being targeted via the CitrixBleed vulnerability in Citrix NetScaler devices.
We don’t have easy ways to check the millions of lines of code and the risks of the technology that we consume. We have to stamp out this blind trust with new tools that can assess digital technology products by understanding their ingredients, how they’re configured, and if they have been altered in any way.
Gartner currently estimates $215 billion will be spent on cybersecurity in 2024, up 14% from 2023, but few of us have confidence that this will meaningfully affect outcomes. That’s because current cybersecurity controls don’t understand this complexity of modern digital supply chains and are thus incapable of addressing the root problem of digital supply chain security. Endpoint security tools are hopefully good at what they do—discovering malware on user endpoints. They have not been designed to deal with the risks of underlying components and ingredients within hardware and software products.
The network scanning tools we use to discover vulnerable network assets similarly have not been designed to understand these devices and software they run “from within,” with visibility into the ingredients devices are made of. They perform surface scans and can’t see deep enough within these assets to understand if they’ve been compromised, and often overwhelm security teams with “critical findings.”
Supply Chain Attacks Are Soaring
If we dive into root causes of most breaches today, we see that incidents involving vulnerabilities in software or hardware products are soaring. Akamai reported that ransomware groups are shifting tactics from phishing and stolen credentials to exploiting vulnerabilities, and said that this shift drove a 143% increase in ransomware victims from Q1 2022 and Q1 2023. Palo Alto Networks Unit 42 has found 48% of ransomware attacks start by exploiting software vulnerabilities.
In 2023 alone, ransomware groups like LockBit, ALPHV, BlackCat, and FIN8, compromised many organizations by targeting vulnerable hardware devices and essential IT software like VMWare ESXi. Hotel and entertainment giant MGM spent $110 million cleaning up after the ALPHV ransomware group compromised its ESXi infrastructure. The Russia-linked LockBit recently added Boeing to the 1,800 victims it has claimed since 2019, claiming to have hacked the aerospace giant by exploiting a zero-day vulnerability. LockBit is known to target IT infrastructure such as F5 Networks and Fortinet appliances and ESXi infrastructure.
Security incidents with wide impact in 2023 have highlighted serious weaknesses in the digital supply chain, such as: vulnerabilities in MOVEit by Progress Software; firmware backdoor capabilities in Gigabyte systems; vulnerabilities in remote management components used by most major server manufacturers; hardware vulnerabilities like Downfall, Zenbleed, and other vulnerabilities in CPU components.
Additionally, ransomware groups also breached major infrastructure vendors including TSMC, MSI, Western Digital, exposing sensitive information about their products, such as signing keys and source code, that could be used by attackers to develop further supply chain attacks.
While ransomware groups threaten serious financial pain for the private sector, state-sponsored threat actors target national infrastructure. BlackLotus, Volt Typhoon, and BlackTech threat actors took aim at the supply chain of PCs, servers, and network devices by multiple manufacturers as initial access vector and to establish persistence.
Geopolitical risks continue to drive concerns of dependency on critical technology developed by foreign manufacturers like Huawei and ZTE. Recently, disk drive components used in U.S. government agencies were found to be manufactured by a company with ties to the PRC’s PLA.
The security of the digital supply chain has taken center stage in U.S. national strategy. Two of the five pillars of the U.S. National Cybersecurity Strategy released in March 2023 are designed to strengthen the transparency and security of software and infrastructure supply chains. Following Executive Order 14028: Improving the Nation’s Cybersecurity, federal authorities including DHS, CISA, NIST, and the NTIA have been driving regulations and guidelines aimed at improving supply chain security.
Introducing the Eclypsium Guide to Supply Chain Security
It can all seem overwhelming. How can we, as an industry, stop placing blind trust in the digital supply chain and start managing the risk, both in applications and infrastructure? How are organizations supposed to demystify complex supply chains that are constantly changing with hundreds of suppliers and sub-suppliers, across dozens of technology vendors?
The first step in this journey starts with supply chain intelligence. Returning to our drink analogy, most of us don’t have a portable kit to test the ingredients in the drink offered. But we would be more likely to accept a drink if we had third-party attestation to the ingredients included, nutritional facts, and any possible risk. Until now, there were no tools available to verify the ingredients in the digital products we use and assess their risk to our infrastructure.
Today we are launching “the standard repository for all knowledge and wisdom” in digital supply chain security. Eclypsium created the Guide to help you begin to navigate the depths of this universe of external digital products and components. We want to arm our customers’ IT and security teams with intelligence and tools to verify the risk and integrity of every hardware, software, and cloud product they use in their infrastructure.
We believe that organizations no longer need to blindly trust hardware and software from their suppliers or treat them as black boxes. Every organization should be able to see and verify what technology is made of before it’s used and after it is deployed. Every organization should be able to understand and control the risk that technologies bring throughout their lifecycle. We believe that securing the Infrastructure Supply Chain is the foundation of every organization’s security. Everything else is built on top of it.
This will change how we manage cyber risk from our suppliers of technology. Assumptions and blind trust will be replaced by verification. At Eclypsium, we are committed to making this a reality together with our customers and partners.
We are starting an early access program for the Guide. If you are interested in getting access and helping us improve it, please let us know.
Don’t Panic!