Why your real-world firmware risk is way bigger than you think
In November 2021, the US Cybersecurity and Infrastructure Security Agency (CISA) began publishing their Known Exploited Vulnerabilities Catalog (KEV). Designed to help government agencies and private sector organizations prioritize the vulnerabilities known to be actively exploited by malicious actors, as of June 22, 2022, the list contains 778 actively exploited CVEs, encompassing 20 years of computing (2002-2022). In fact, CISA recommends these KEVs be addressed even prior to other High or Critical vulnerabilities that are not yet known to be exploited, citing the fact that less than 4% of vulnerabilities are ever exploited in the wild. With more than 20,000 CVEs discovered in 2021 alone, the KEV gives organizations a highly distilled list of vulnerabilities that are most likely to have a real-world impact based on observed actions in the wild.
So important are the KEVs, that a new Binding Operational Directive 20-01 – Develop And Publish A Vulnerability Disclosure Policy requires Federal Civilian Executive Branch agencies (aka FCEBs) such as the DOJ, DOT, DHS, DOE, GSA, SEC etc., to implement entire vulnerability management programs built around it, along with auditable documentation that is publicly visible to all. An example of the changes enforced by this order would be the DOJ’s VDP page here, which outlines the DOJ’s Vulnerability Disclosure Program.
Note that while the BOD does not directly require private/commercial entities that sell into these FCEBs to create a VDP and prioritize KEVs, it is suggested that they might do so.
“Although not bound by BOD 22-01, every organization, including those in state, local, tribal, and territorial (SLTT) governments and private industry can significantly strengthen their security and resilience posture by prioritizing the remediation of the vulnerabilities listed in the KEV catalog as well.”
Security trust and parity across organizations and the vendors that sell their software and devices into them is paramount to national security. Private organizations would be wise to leverage the significant DFIR telemetry, FBI and Fusion Center telemetry, researcher and trust-community initiatives in place, and the overall publicly funded effort it takes to curate the KEVs; as a defensible, actionable, and structured approach to vulnerability risk management.
CISA itself does not yet categorize the vulnerabilities, so we augmented their list by assigning categories to each vulnerability to get a better understanding of the types of assets and code that threat actors are targeting the most.
- Firmware (e.g. Intel AMT, Cisco, F5 Networks)
- Server Software (e.g. Apache, Microsoft Exchange)
- Operating Systems (e.g. Windows, Android)
- Web Browser (e.g. Google Chrome, Internet Explorer)
- Office applications (e.g.. Microsoft Word, Excel)
- Applications (e.g. WinRAR, WhatsApp)
- Software library (e.g. OpenSSL)
- Virtualization (e.g. Docker, VMWare)
By categorizing each vulnerability, we are able to identify exploitation trends over the last 20 years which gives some perspective into the evolution of attacker targets.
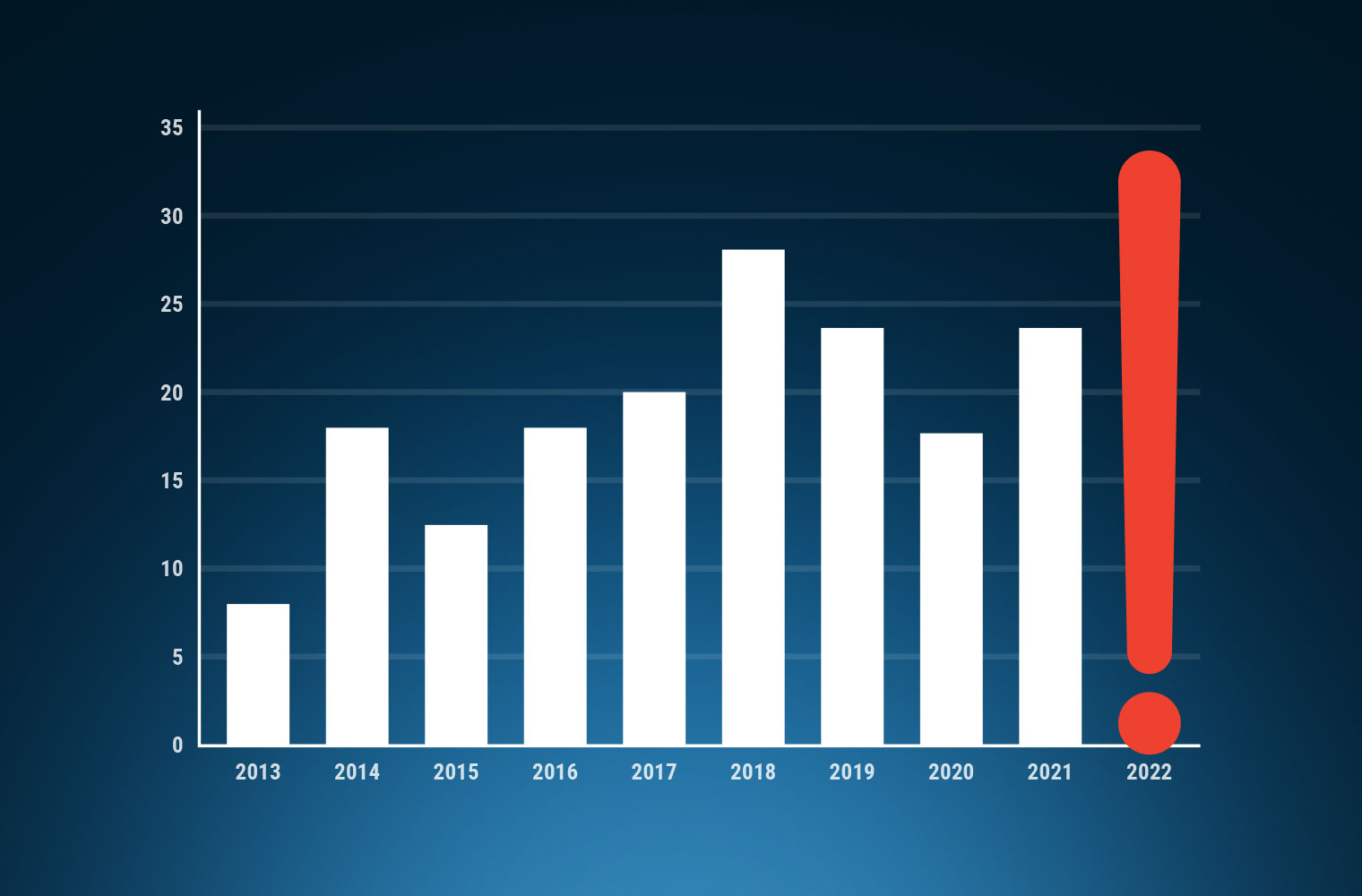
Trended over time, it is no surprise to see the number of actively exploited vulnerabilities increasing year over year, and it’s important to note that CISA adds vulnerabilities as exploitation is detected. As a result, the number of exploited CVEs in a previous year could climb based on the data CISA has available.
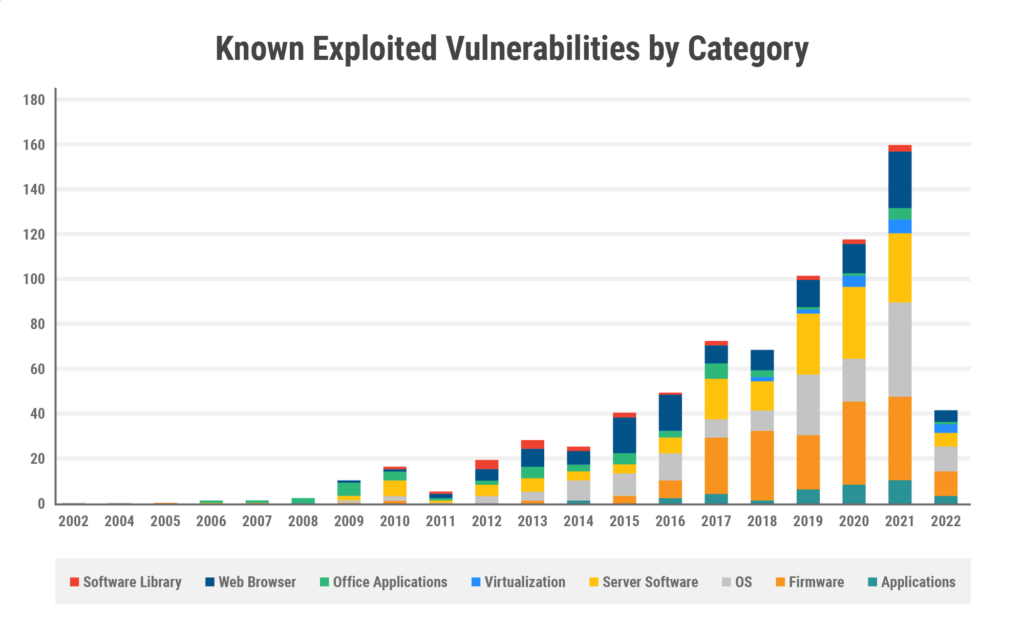
In terms of categories, firmware led the way overall, followed by server software, operating systems, and web browsers. Let’s analyze each category in more detail.
| Category | Count |
| Firmware | 184 |
| Server Software | 168 |
| OS | 161 |
| Web Browser | 127 |
| Office applications | 51 |
| Applications | 43 |
| Software Library | 24 |
| Virtualization | 20 |
Firmware
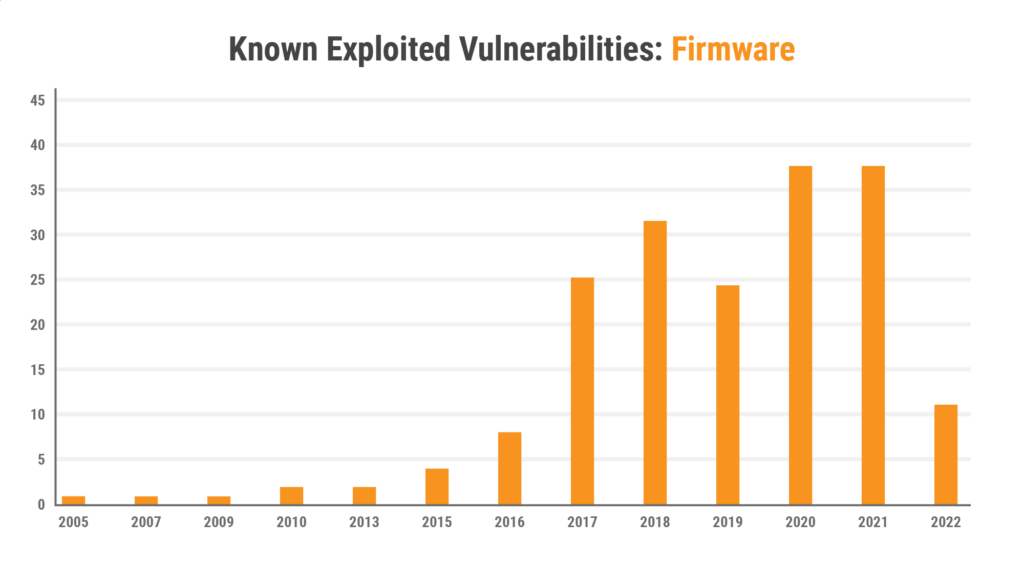
While the prevalence of firmware-based CVEs may be a surprise to some, it is a reflection of the large-scale shift of adversaries targeting firmware within enterprise and network infrastructure. It’s also important to note that the numbers aren’t skewed simply due to an anomalous spike in the data. Firmware has been one of the leading categories of vulnerabilities over the past 5 years and continues to be thus far for 2022. Firmware is the leading category over virtually any time horizon we choose.
| Applications | Firmware | OS | Server Software | Virtualization | Office Applications | Web Browser | Software Library | Grand Total | |
| Last 2 | 15 | 48 | 53 | 37 | 10 | 6 | 30 | 3 | 202 |
| Last 3 | 24 | 85 | 72 | 69 | 15 | 7 | 43 | 5 | 320 |
| Last 4 | 31 | 109 | 99 | 96 | 17 | 8 | 55 | 7 | 422 |
| Last 5 | 33 | 140 | 108 | 109 | 19 | 11 | 64 | 7 | 491 |
| Last 6 | 38 | 165 | 116 | 127 | 19 | 18 | 72 | 9 | 564 |
| Last 7 | 41 | 173 | 128 | 134 | 19 | 21 | 88 | 10 | 614 |
| Last 8 | 41 | 177 | 138 | 138 | 19 | 26 | 104 | 12 | 655 |
| Last 9 | 43 | 177 | 147 | 142 | 19 | 29 | 110 | 14 | 681 |
| Last 10 | 43 | 179 | 151 | 148 | 19 | 34 | 118 | 18 | 710 |
| All time | 47 | 184 | 161 | 164 | 20 | 51 | 127 | 24 | 774 |
This is a troubling trend for many organizations given that traditional vulnerability management programs often don’t reach down to the firmware level. Firmware makes up the foundation of modern computing, running on every device before the operating system even loads.very computer contains multiple components like CPU, memory, network adapter, video cards, and hard drives and each of these components contains firmware, difficult to monitor due to running at a level below the operating system. The compromise of firmware can provide an attacker with persistent access, even if the operating system is fully reinstalled or even if the hard drives are replaced.
While it is one thing to acknowledge these firmware vulnerabilities are “known to be exploited”, it is quite another to realize that the actors behind these active attacks are some of the most prolific and notorious there are, and responsible for some of the longest-running campaigns against both government and critical infrastructure. While the table of KEVs does not specifically identify (aka ‘attribute’) a given actor with a given vulnerability that’s been exploited, it is easy enough to infer by simply reviewing the long list of recent CISA advisories, or even their high-level “Shields Up!” initiative. There, the reader can gain a much deeper insight into the campaigns and TTPs (Tools, Tactics, Procedures), leveraging vulnerabilities to meet their objectives. Well known Russian and Chinese nation-state sponsored attacks, as well as cyber criminal and ransomware actor groups, as well as attacks against our software supply chain, managed service providers, telecom infrastructure, hospitals and more. The initial vector into the attacked organizations is more often than not, the firmware of externally-facing devices such as routers, firewalls, VPN devices, and soho devices. Equally apparent, is that these same actors are also leveraging vulnerable firmware on devices internal to the network in order to persist, gather credentials, tunnel C2 (command and control) and exfiltrate data.
Network devices also run firmware, and while they also run an operating system, unlike desktops and servers they lack the advanced security tooling deployed across many enterprises. Due to their mission criticality, they are extremely high-value targets as they can be leveraged to further breach a network, monitor or redirect traffic, or even shut down large parts of the Internet.
Server Software
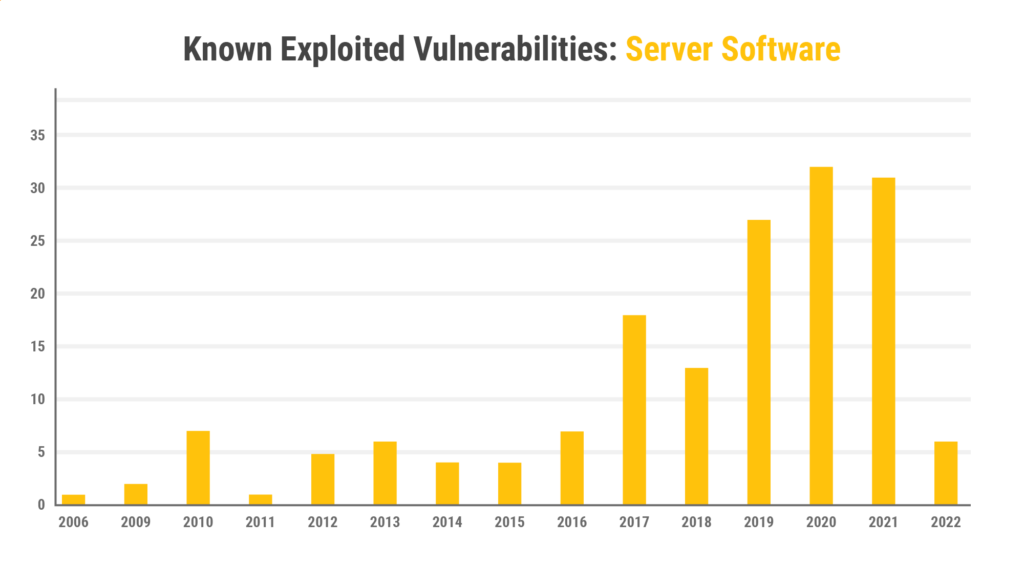
Servers are naturally high-value targets for attackers as they frequently store large amounts of sensitive data such as email, databases, code repositories, and customer data. In 2017, the MS17-010 vulnerability in SMB Server facilitated both the WannaCry and NotPetya cyber attacks, causing billions of dollars in damage, shutting down shipping ports, and impacting businesses worldwide. Likewise, threat actors have notably exploited vulnerabilities in Microsoft Exchange Server in order to steal confidential information and deploy ransomware. Most recently, the industry experienced widespread attacks against Atlassian Confluence Server by attackers using a previously unknown vulnerability (CVE-2022-26134) affecting all versions of Confluence Server.
Operating Systems
Operating systems serve the end-user(s) and applications on a given device, and any compromises to the OS can give attackers access to data and privileges, and open additional vectors of attack. Threat actors can use this access to maintain persistence, move laterally to other hosts, steal data, and deploy ransomware.
Securing and monitoring operating systems for compromise has become a multi-billion dollar industry, evolving from basic antivirus software in the 1990’s to current cloud-based solutions which monitor every action on the system in an attempt to catch patterns of events known to be malicious.
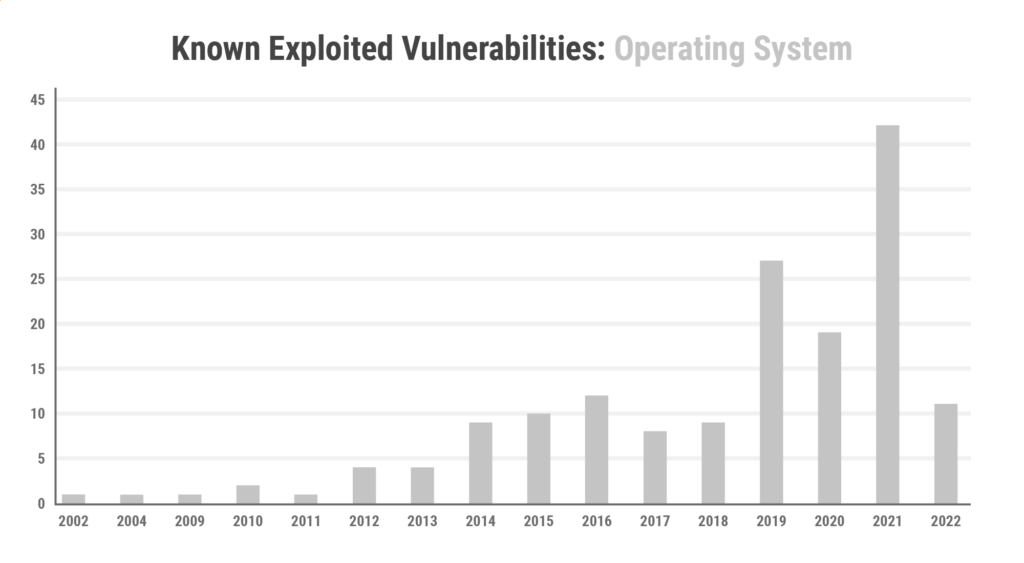
Operating system vendors have improved over the years in terms of providing automated updates to ensure that any vulnerabilities are mitigated quickly in order to reduce their exposure to threat actors. Yet in spite of these efforts, OS vulnerabilities continue to be popular with threat actors including 42 vulnerabilities from 2021 alone. These vulnerabilities were mostly spread across versions of Windows operating systems and Apple’s iOS.
Web Browsers
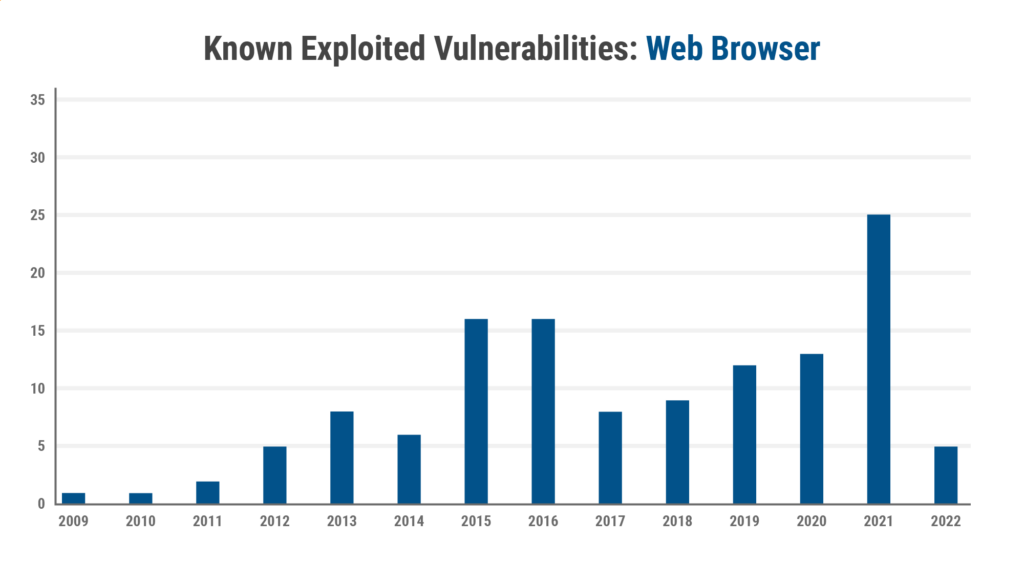
As the majority of applications have shifted to the browser, so too has cybersecurity risk. Virtually all of a user’s experiences are delivered through a browser, and users can easily use dozens or even hundreds of web-based sites and applications in a given day. This creates a target-rich environment for attackers, who can lure users into risky clicks or use automated exploit kits to deliver malware to vulnerable browsers.
Browser CVEs have proven to be popular in the wild with attackers. In particular, vulnerabilities in Google Chrome were found to be popular such as CVE-2021-21224, which was targeted by the Magnitude Exploit Kit.
Office Applications
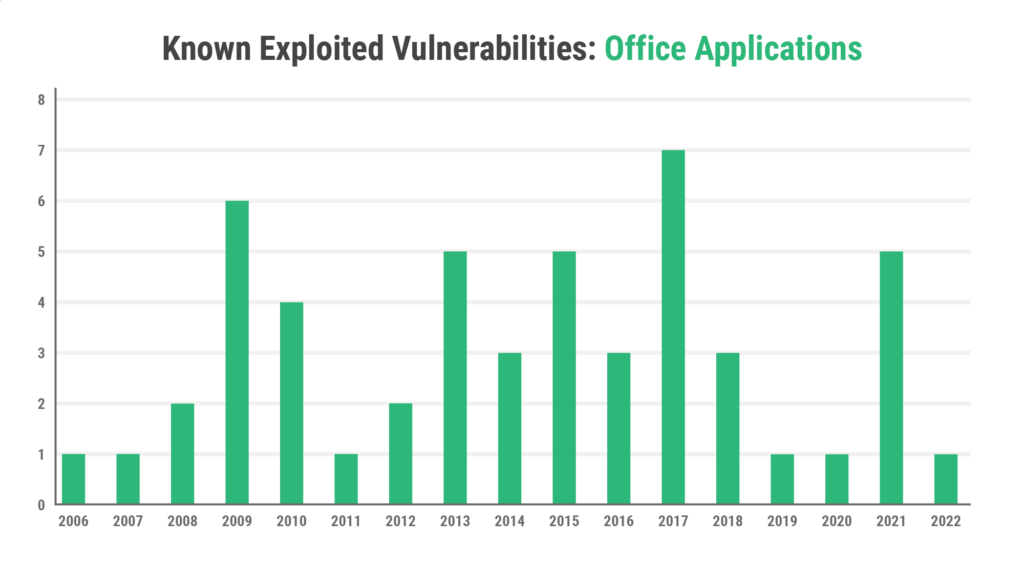
End-user applications such as the Microsoft Office suite and Adobe Acrobat have long been targeted by attackers. Vulnerabilities in these applications can allow an adversary to gain code execution by luring users into opening a malicious file and have been a mainstaying of phishing campaigns for many years. Notably, the KEV catalog includes the Microsoft vulnerability CVE-2022-30190, which can be exploited by an attacker even if the user does not open the malicious file.
In order to maximize their targets, attackers have naturally focused on applications that are virtually ubiquitous. This has made Adobe Acrobat and Acrobat Reader particularly popular targets. For example, the recent Adobe vulnerability, CVE-2021-28550, was first observed in the wild as a 0-day vulnerability, allowing attackers to gain arbitrary code execution on a victim device.
Applications
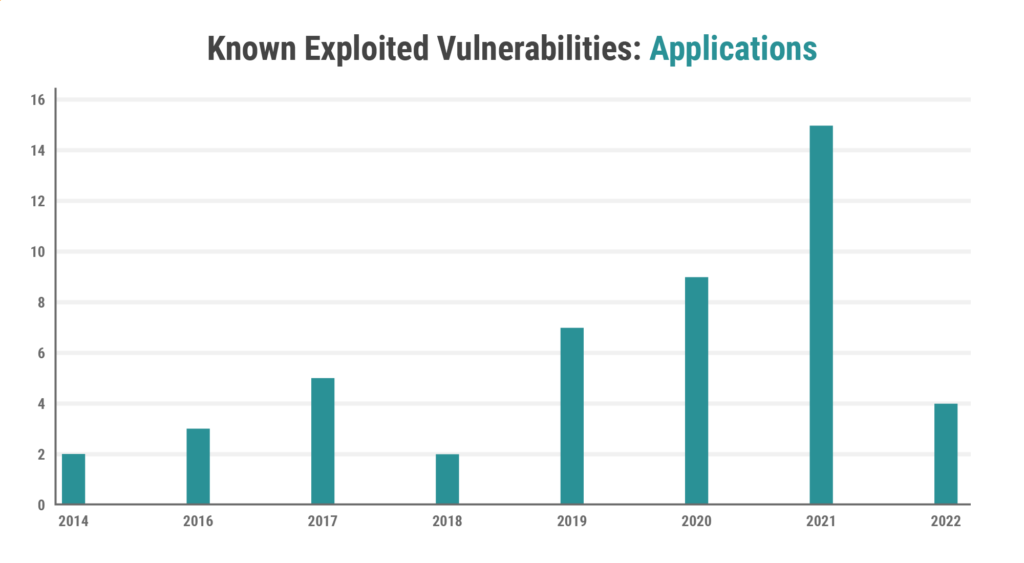
While much of modern computing runs in a web browser, users and organizations still rely on a variety of traditional desktop applications. Popular chat applications like WhatsApp have been targeted by companies like NSO Group, who famously used a zero-day exploit to compromise and subsequently spy on Amazon CEO, Jeff Bezos. The KEV catalog includes multiple WhatsApp vulnerabilities including CVE-2019-3568 and CVE-2019-18426, as well as vulnerabilities in common applications such as Team Viewer Desktop.
Software Library
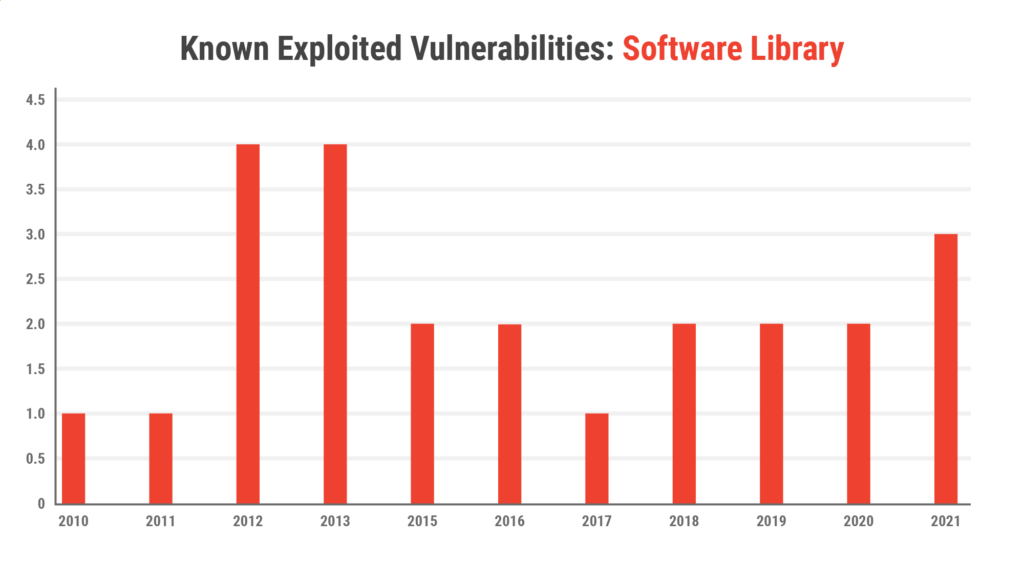
Open source software has become an essential part of modern application development, allowing developers to quickly integrate capabilities into their applications and projects. However, this widespread reuse of code means that vulnerabilities in open source projects can likewise be incorporated into countless applications. For example, the notorious Heartbleed vulnerability in the OpenSSL library affected hundreds of thousands of devices globally. More recently, in December 2021, a remote code execution vulnerability in the popular Log4j library came under widespread exploitation. A Neustar International Security Council (NISC) survey indicated an estimated 60% of organizations had been targeted through this vulnerability. CISA also released an alert on June 23rd 2022 warning organizations that malicious actors have been using the Log4j exploit to breach VMWare servers before moving laterally inside the network.
Additionally, attackers have begun employing a new tactic: inserting malicious code into popular libraries. While it is hard to quantify the number of successful attacks resulting from this tactic, GitHub has updated its advisory database to include malware found in open source projects.
Virtualization
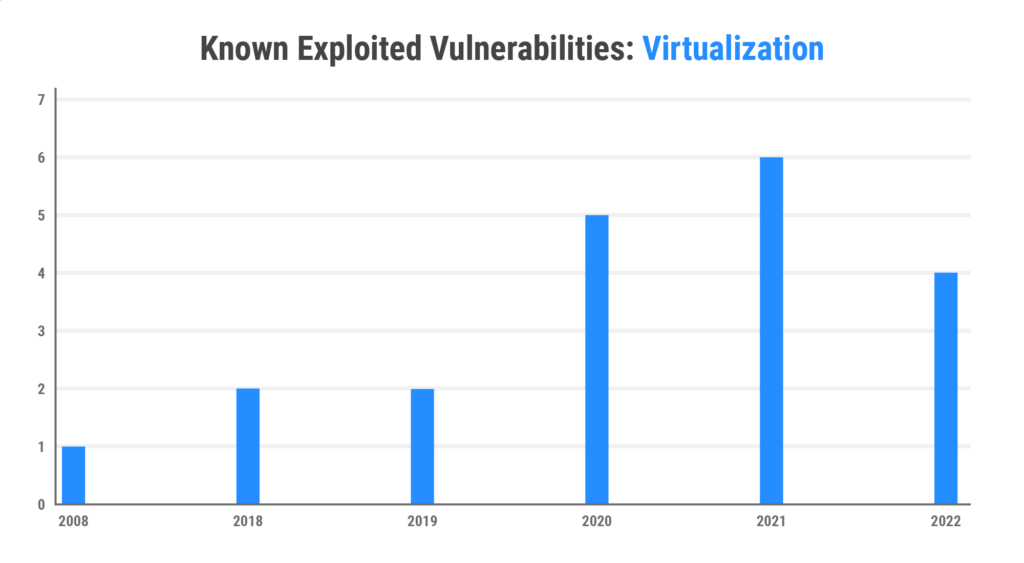
Virtualization is a relatively new attack vector in computing, and due to the rapid rise of cloud computing and containerization is one that will likely increase. However, much like attackers have targeted the execution environment of operating systems, they can similarly target the virtual environments and containers that support modern workloads. Vulnerabilities in these areas are potentially significant as they can allow an attacker to escape the virtualized environment and gain control over the physical host. The recent exploitation of the VMware vulnerability, CVE-2022-22960, provides a case in point.
Conclusions
Ultimately an organization’s cybersecurity strategy must be informed by the risks and threats observed in the real world. CISA’s KEV catalog is a powerful tool, arming security teams with insight into the vulnerabilities that matter most.
When it comes to firmware, there is an opportunity for organizations to see an area where they are likely under-appreciating their risk. The KEV data indicates that firmware has become a top target for real-world adversaries. This could be due to the powerful and strategic nature of firmware itself, or the fact that firmware often does not get updated and patched with the same rigor as other forms of code, or a combination of the two. However, regardless of the motivation, the data shows that firmware has consistently been an area of focus in real-world attacks, and it is up to security teams to build the processes to ensure the posture and integrity of their critical firmware.
For any questions, regarding the data in this post or to learn more about firmware security, please contact the Eclypsium team at [email protected].